Twitter Feed
US Army Cloud Computing Class at Ft. Gordon, GA
A few weeks ago I had the distinct pleassue of teaching yet another US Army cloud computing class. This time the venue was Ft. Gordon, GA and the students definitely…
78 Agency Services Identified for Cloud Transition
The Office of Management and Budget recently released a list of 78 projects slated for transition to cloud over the next year. The most common application, according to a FierceGovernmentIT,…
NGA Sets GEOINT Strategic Direction with Earth Builder
Last month Google and the National Geospatial Intelligence Agency started sharing details about their “GEOINT on Demand” collaboration. The project, named Earth Builder, was built specifically to enable NGA to…
Teleology Systems Introduces CloudeFX at DoDIIS
Next week at DoDIIS, NJVC will be showcasing a few of our government cloud computing partners. One of the most exciting of these is the Cloud Service Orchestration Framework by…
Cloud Computing Highlighted at DoDIIS 2011
Are you going to DoDIIS? Schedule for May 1-5, 2011 in Detroit, Michigan, the conference highlights the Defense Intelligence Agency’s (DIA) commitment to developing and maintaining secure and reliable networks for…
Washington DC a Cloud Computing Trendsetter!
A TechJournal South article last week named Washington, DC as a leading trendsetter in cloud computing. Citing a Microsoft sponsored survey, conducted by 7th Sense research, D.C. was highlighted as particullarly receptive…
Melvin Greer Cited by IBM for Cloud Computing Innovation
Congratulations to my good friend Melvin Greer for being awarded IBM’s first ever ACE Award!! “Melvin Greer, Lockheed Martin Senior Fellow has won IBM’s first ever Awarding Customer Excellence (ACE)…
“GovCloud: The Book” Launched at National Press Club Event
As many of you know, today marked the official launch of my first book – GovCloud: Cloud Computing for the Business of Government. Today’s venue was the National Press Club…
“Cloud Musings on Forbes” Launched!!
Today I published my first post on Forbes.com!! At the invitation of Bruce Upbin, Forbes.com editor, I will be contributing posts monthly. I see this not only as an honor,…
Tech America and INSA Form Cloud Computing Advisory Groups
Last week TechAmerica announced the formation of a “cloud computing commission” to advise the White House on the current plans to steer more than $20B worth of IT services toward…
According to the National Institute of Standards and Technology:
“Cloud computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications and services) that can be rapidly provisioned and released with minimal management.”
While this definition is broadly accepted and has, in fact, been my adopted standard for years, it only describes technical aspects of cloud computing.
The amalgamation of technologies used to deliver cloud services is not even half the story. Above all else, the successful employment requires a tight linkage to the economic and business models of the enterprise. Critical components for any transition to cloud include:
- Enterprise economic model
- Organizational goals (financial and operational)
- Enterprise operational model
- Relevant operational processes
- Relevant operational resources
- Process relevant data
- Data classification (e.g. severity of enterprise damage if the data is used improperly)
- Risk identification and management
- Security controls
- Process automation
Taking all of these components in total, cloud computing is a business model for propelling an enterprise towards its economic and operational goals. This is why cloud computing transitions cannot be left as a task for the information technology team.
The most central aspect of any business is data because data is the fuel for all business processes. The custodian of this data is the business owner. The technical aspects of cloud computing are only tools for the provisioning, manipulating and storing of data. Decisions on all aspects of any cloud computing deployment must therefore be purposely driven by business process owners. The IT Team acts as the trusted technology advisor to and the technology execution arm of the business process owners. On the flip side, the business process owner must act as the trusted business advisor to and business execution arm of the IT Team. This defines why collaboration is essential in the delivery of a cloud computing solution. It also explains why the object of this collaboration must be business data.
Data-centric collaboration explicitly addresses how an organization handles each business data-type throughout its lifecycle. In recommending industry best practices for security, the International Information System Security Certification Consortium, would recommend the use of the data security lifecycle:
- Create: The generation of new digital content or the alteration/updating/modifying of existing content. This phase can happen internally in the cloud or externally and then the data is imported into the cloud. The creation phase where data classification and encryption is implemented. During this lifecycle phase, data can be vulnerable to attackers if access control list are not well implemented or enforced. Correct threat scanning processes and data classification are also critical.
- Store: The act of committing digital data to a storage repository typically occurs nearly simultaneously with creation. Controls such as encryption, access policy and backups should be implemented to avoid data threats.
- Use: Data is viewed, processed, or otherwise used in some sort of activity, not including modification. Data in use is most vulnerable because it is might be transported into unsecure location. Controls such as DLP (digital loss prevention), IRM (information rights management) and database and file access monitors should be implemented in order to audit data access and prevent unauthorized access.
- Share: Information is made accessible to others. Not all data should be shared, and not all sharing should present a threat. Since shared data is no longer in control of the organization, this is a very challenging phase to perform securely. Technologies such as DLP can be used to detect unauthorized sharing, and IRM technologies can be used to maintain control over the information.
- Archive: Data leaves active use and enters long-term storage. Cost vs. availability trades based on business considerations must drive data access procedures. Regulatory requirements must also be addressed.
- Destroy: The data is removed from the cloud provider. Destruction options are driven by usage, data content and applications. Data destruction can mean logical erase of pointers or permanently data destruction using physical or digital means.
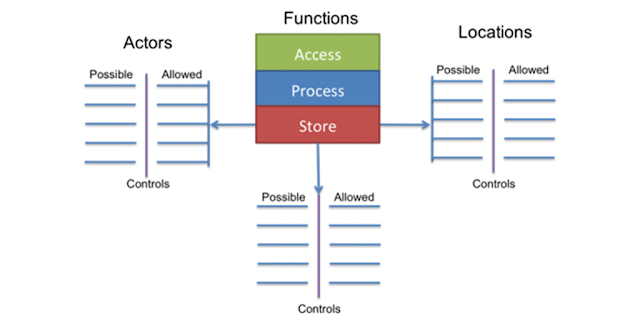
The handling of each datatype should also be defined in terms of:
- The actors that potentially have access to the data;
- Potential locations for the data;
- The types of security controls present in each potential location; and
Allowable functions in each potential location include:
- Access: View/access the data, including copying, file transfers, and other exchanges of information;
- Process: Perform a transaction on the data: update it, use it in a business processing transaction, etc.; and
- Store: Store the data (in a file, database, etc.).
The data-centric approach is crucial as more enterprises adopt the hybrid cloud model. According to Gartner, nearly half of all large enterprises will have hybrid cloud deployments by the end of 2017. Dell, in fact, lists security and management as one of five essential consideration for hybrid cloud saying that, “Customers can now manage their own encryption keys when using a public cloud data store, and vendors like Dropbox, OneDrive and others can integrate with IT systems so that data is transparently encrypted on its way from users’ workstations to public cloud services without any additional steps on the part of the end user.”
A data-centric business model abandons the typical infrastructure-centric security model by adopting an explicit assumption that the IT infrastructure cannot be trusted to protect business data. Embedded in that assumption are also requirements for the encryption of all data-at-rest, data-in-motion and, if possible, data-in-use. An effective transition to cloud computing demands the adoption of a data-centric business model and the equally important broad use of encryption technologies.
This post was written as part of the Dell Insight Partners program, which provides news and analysis about the evolving world of tech. Dell sponsored this article, but the opinions are my own and don’t necessarily represent Dell’s positions or strategies.
( Thank you. If you enjoyed this article, get free updates by email or RSS – © Copyright Kevin L. Jackson 2015)
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes