Twitter Feed
SourceConnecte! Marketplace With A Mission
Earlier this year, GC GlobalNet launched a new breed of B2B e-commerce sites. Curated by Kevin L. Jackson, SourceConnecte (with an “eâ€) went live with three strategic goals in mind: Efficiently leverage modern…
Potential vs. Reality: Is Edge Computing Real?
Edge computing provides compute, storage, and networking resources close to devices generating traffic. Its benefits are based on an ability to provide new services capable of meeting stringent operational requirements…
Enabling Digital Transformation
Digital transformation integrates technology into all areas of an organization’s business or mission. Its fundamental purpose is to create and deliver innovative and industry-changing products and services to a global…
The ThinkShield Story Part 1: The Challenge
The cybersecurity challenge seems to be growing daily. Threats are becoming more sophisticated, and attacks are becoming more destructive while the corporate world’s response seems to resemble a deer…
CIO dream team: Who’s in and why?
Today’s CIO navigates the twin challenges of enabling new business models and managing rapid technological change. Cloud computing strategies are now table stakes. CIOs must make complex decisions about using…
Digital Transformation and the Mainframe
Digital transformation infuses digital technology into all areas of an organization’s business or mission. Its fundamental purpose is to create and deliver innovative and industry-changing digital products and services to…
Composable Architecture Q&A. Are you ready?
Q: Is it time for my company to jump on the composable architecture bandwagon? A: Composable architectures are quickly becoming essential to the modern enterprise. Citing a recent Forrester study:…
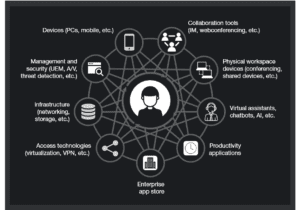
Increase Productivity by Reducing Technology Distraction: Lessons from Forrester Research
Workplace productivity is hurt every day by the very technology developed and purchased to improve it. Forrester announced this surprising conclusion in their latest “How To Wake Up From The Nightmare…
Unveiling the end-to-end capabilities for the networked society
An Interview with Henrik Basilier By Kevin L. Jackson The telecom industry is rapidly moving towards a future in which networks must have the capabilities of delivering services with the…
AT&T Finance Solutions GM on Shrimping, Software, and CX
Helping clients address the trends and challenges presented by the Financial Services industry is the main focus for René Dufrene in his role as General Manager of Finance Solutions at…
- Rise of the “Cloud System Integrator” (a.k.a. Cloud Service Broker) – Traditional system integrators will finally realize that their current product and labor based business model is about to go the way of the dinosaurs. Customers will act on market shifts that makes the purchase and resale of hardware and software no longer viable opting instead for the integration of cloud-based services. They will insist on the use of more agile commodity IT services in the development of their custom systems of record.
- Privacy will be more important than security – Expect the national debate about data privacy to escalate into a new national law that defines privacy and provides cloud users new protections from data brokers. Identity will be the new security perimeter for consumers of cloud services. As the United States Department of Homeland Security rolls out Phase II of the Continuous Diagnostics and Mitigation Program, multinational corporations across all industries will take notice.
- Wearables will become the most impactful mobile device – BYOW will replace BYOD as the primary concern of enterprise IT managers.
- Linux Containers take center stage – Linux Containers of all forms, will mature and become interoperability building blocks of the cloud computing world. The Microsoft-IBM Cloud Computing Alliance will be model as other IT behemoths partner to take down Amazon Web Services.
-
 Hybrid IT grows in the enterprise – Hybrid IT will grow in importance as enterprises realize that the exclusive use of private IT infrastructure is no longer a sustainable practice. Membership in industry specific community clouds will accelerate as public cloud security is improved and SLAs are enhanced to meet new government IT security standards and requirements.
Hybrid IT grows in the enterprise – Hybrid IT will grow in importance as enterprises realize that the exclusive use of private IT infrastructure is no longer a sustainable practice. Membership in industry specific community clouds will accelerate as public cloud security is improved and SLAs are enhanced to meet new government IT security standards and requirements. - Social Media takes over – Social media will usurp other forms of marketing to become the leading tool for influence marketing and initial customer contact. Today the average Fortune 100 brand has 320 social media accounts. This will grow and the social media marketing trend will spread down into the SMB market. As cloud enabled social media analytics grow in importance, the Chief Marketing Officer will become the leading internal stakeholder and voice in directing IT requirements.
- International Cyber Security Regulations – The lack of mandatory cyber security requirements in the commercial sector will rise to threaten national economic stability as hackers expand their activities and ability to disrupt commerce on a global scale. International political bodies will finally tackle the need for global agreements on data privacy and security
 Data center marketplace disruption – The data center marketplace will experience severe disruption as global cloud service providers start to deploy offshore mega data centers. Driven by reduced energy cost and a more tractable legal environment, onshore data centers will be downsized into regional “data caching centers”.
Data center marketplace disruption – The data center marketplace will experience severe disruption as global cloud service providers start to deploy offshore mega data centers. Driven by reduced energy cost and a more tractable legal environment, onshore data centers will be downsized into regional “data caching centers”.- Healthcare gets REALLY personal – Drastic reduction in the cost to sequence DNA will spur a rapid rise in personalized medicine and an adjacent requirement for real-time health monitoring. Wearable computing devices will be miniaturized and implanted as a means for addressing this new market.
 Autonomous vehicles become commonplace – Autonomous vehicles will become a normal roadway and airway fixture as broadband wireless connectivity, advanced geospatial services and on-board computer processing power increases their capabilities and reduces their cost. Legal concerns will also take center stage. The use of airborne drones, for instance, will bump upagainst privacy concerns as neighbors start to spy on neighbors.
Autonomous vehicles become commonplace – Autonomous vehicles will become a normal roadway and airway fixture as broadband wireless connectivity, advanced geospatial services and on-board computer processing power increases their capabilities and reduces their cost. Legal concerns will also take center stage. The use of airborne drones, for instance, will bump upagainst privacy concerns as neighbors start to spy on neighbors.- 3D Printing comes home – Additive manufacturing will come home as a household appliance. Business models that incorporate the cost of 3D printers into home mortgages or long term leases will revolutionize certain product market segments. Online shopping, purchase, and the digital delivery of physical products will become a reality
- Atoms and Bits blur reality – Business models that blur the boundaries between atoms and bits, like Uber and AirBNB, will continue to challenge municipal laws and regulations. Local licensing of taxis, hotels and similar businesses will implode under the weight of digital transformation. Regional and national courts around the world will try to balance competing priorities but time will be their enemy.
(This post was written as part of the Dell Insight Partners program, which provides news and analysis about the evolving world of tech. To learn more about tech news and analysis visit TechPageOne. Dell sponsored this article, but the opinions are our own and don’t necessarily represent Dell’s positions or strategies.)
( Thank you. If you enjoyed this article, get free updates by email or RSS – © Copyright Kevin L. Jackson 2012)
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes