Twitter Feed
Lynn DeCourcey Showcased in ExecutiveBiz
Kudos to my colleague Lynn DeCourcey for her recent interview on ExecutiveBiz.com! Lynn is NJVC vice president and general manager, cyber security. She oversees all aspects of the company’s cyber…
BISNOW Data Center Event Highlight’s Cloud
A big thank you to BISNOW and my fellow panel members for an outstanding discussion and very informative event, last week’s Data Center Investment Conference and Expo. The federal marketplace…
GSA Seeks Cloud Brokerage Information
GSA is using the RFI process to collect information about alternative models and/or solutions for future cloud acquisition vehicles and processes that further these goals. One emerging concept in cloud…
DoD Cloud Computing Strategy
The DoD recently released the department’s formal cloud computing strategy. DoD Cloud Computing Strategy View more documents from Kevin Jackson. In the forward, DoD CIO Teresa Takai said that: “The…
FedRAMP PMO Releases First Set of 3PAOs
Late today the FedRAMP Program Management Office released the first list of certified Third Party Assessment Organizations (3PAOs). These companies are accredited to perform initial and periodic assessment of cloud…
FedRAMP Releases Updated Security Assessment Plan Templates
Last week the GSA FedRAMP Program Office released the latest version of the cloud computing Security Assessment Plan (SAR) template. This document is the most recent step toward the Federal…
NJVC® and Gravitant® Announce New Strategic Alliance: Partnership to Benefit Federal Agencies with Powerful Provision and Management of Cloud Services that Unify Multiple Providers
Vienna, Va., April 4, 2012 — NJVC®, one of the largest information technology solutions providers supporting the U.S. Department of Defense, and Gravitant®, a provider of cloud brokerage and management…
NJVC® VP and GM, Cloud Services, Kevin L. Jackson to Speak on Cloud Security at 2012 Emerging Threats and Cyber Defense Symposium
Vienna, Va., March 15, 2012 — NJVC®, one of the largest information technology solutions (IT) providers supporting the U.S. Department of Defense, is pleased to announce that Kevin L. Jackson,…
NJVC’s Kevin L. Jackson Co-Authors INSA White Paper on Cloud Computing for the Intelligence Community
Findings Reflect Insight from More than 50 Cloud Thought Leaders VIENNA, Va.–(BUSINESS WIRE)–NJVC®, one of the largest information technology solutions (IT) providers supporting the U.S. Department of Defense, announces…
INSA Study on Cloud Computing in the Intelligence Community: Rollout 13 March 2012 | SYS-CON MEDIA
(Originally posted by Bob Gourley at CTOvision) Over the last year I’ve had the pleasure of serving with a team of volunteers from the Intelligence and National Security Alliance…
A recently released infographic from CloudCheckr (https://cloudcheckr.com/) sheds quite a bit of light on the importance of expert advice when an enterprise decides to deploy to the cloud. When AWS made Trusted Advisor free for the month of March, they took that opportunity to conduct an internal survey of their customers’ usage. CloudCheckr compared the initial scans of 400 users against a list of 125+ best practice checks. The survey was limited to users with over 10 EC2 instances. In aggregate, the users represent a total of just over 16,000 EC2 instances.
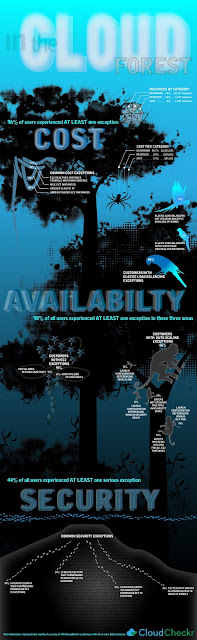
Specific conclusion as provided by CloudChekr, are :
- 96% of all users experienced at least 1 cost related exception(with many experiencing multiple exceptions).
- Price optimization remains a large hurdle for AWS users
- Nearly 98% suffered from at least 1 availability related exception.
- 44% of our users had at least one serious security related exception present
- Spot instances worry users – there is a general concern of: “what if the price spikes and my instance is terminated?” This fear exists despite the fact that spikes occur very rarely, warnings are available, and proper configuration can significantly mitigate this “surprise termination” risk.
- It is difficult and time consuming to map the cost scenarios for purchasing reserved instances. The customers who did make this transition had cobbled together home grown spreadsheets as a way of supporting this business decision.
- The intricacies of matching the configurations between on demand instances and reserved instances while taking into consideration autoscaling and other necessary configurations were daunting. Many felt it was not worth the effort.
- Amazon’s own process for regularly lowering the costs is a deterrent to purchasing RIs. This is especially true for RIs with a 3 year commitment. In fact, within the customers who did purchase RI, none expressed a desire to commit to 3 year commitments. All supported their refusal by referencing the regular AWS price drops and the fact that they could not accurately predict their business requirements 3 years out.
- Users were generally surprised with the exceptions. They believed that they “had done everything right” but then realized that they underestimated the complexity of AWS.
- Users were often unsure of exactly why something needed to be remedied. The underlying architecture of AWS continues to unfold and users are not always familiar with the latest AWS twist.
- AWS dynamism played a large role in the number of exceptions. Users commented that they often fixed exceptions and, after a week of usage, found new exceptions had arisen.
- Users remained very happy with the overall level of service from AWS. Despite the exceptions which diminish overall functionality, the users still found that AWS offered tremendous functionality advantages.
SECURITY
- The AWS management console offered little functionality for helping with S3 security. It does not present a useful means of monitoring and controlling S3 inventory and usage. In fact, we found that most of our users were surprised when the inventory was reported. They often had 300-500% more buckets, objects and storage than they expected.
- S3 is often an afterthought for users. EC2 commands more user attention. Users often failed to create and implement formal policies.
- S3 cost was contributing to factor to the problems. Given the low cost, team members throw up objects and buckets at will while secure in the knowledge that they can store huge amounts of data at a minimal cost. Similarly, the low costdisincentives users to perform inventories from each region and perform an audit of objects and policies/configurations. Since users did not know what they had stored, they could not determine the level of security.
( Thank you. If you enjoyed this article, get free updates by email or RSS – © Copyright Kevin L. Jackson 2012)
1 Comments
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes


Hi Everyone,
I'm Aaron Klein a co-founder of CloudCheckr. I hope you found the results of our survey interesting and informative. If you are curious to see how well your AWS account is configured, we'd like to invite you to set up a free account on CloudCheckr. You just need to enter read only credentials from your AWS account into CloudCheckr, and within a few minutes, you can see how well you scored against our best practice checks: https://app.cloudcheckr.com/LogOn/Registration