Twitter Feed
AFCEA: Cyberspace at the Cross Roads
Starting December 2, 2009, the Armed Forces Communications and Electronics Association (AFCEA) will be putting on a two-day cyberspace conference. Titled “Cyberspace at the Cross Roads: The Intersection of Cyber,…
“Cloud” Shows Promise during Navy Trident Warrior
Last month as part of the Navy’s annual Trident Warrior exercise, Dataline, LLC successfully demonstrated that a standard shipboard communications infrastructure could be used to manage a commercial cloud infrastructure-as-a-service…
Government Cloud Computing Value Survey
As part of a continuing Government Cloud computing education program, Dataline, LLC has released a Government Cloud Computing Value Survey. This online resource has been designed as an aid to…
“Hyper-Standardized” Cloud Computing Environment a Plus for DISA
Henry Sienkiewcz, DISA Computer Services Technical Director, credits the cloud computing “hyper-standardized” environment for the improvement they have been able to deliver through their cloud computing initiative. During remarks at…
Army Deputy CIO Cites Army/DISA Cloud Computing Partnership
This week’s Federal Executive Forum taping highlighted collaboration between DISA and the Army on the service’s transition to cloud computing. Army Deputy Chief Information Officer Mike Krieger called it a…
Navy CIO Discusses Cloud Computing
During this week’s Federal Executive Forum taping, Navy CIO Robert Carey discussed his views on cloud computing. Stating that the NGEN and CANES (Navy Consolidated Afloat Networks and Enterprise Services)…
DoD, DHS and FBI Highlight Identity Management Interoperability
During this week’s Federal Executive Forum, key decision makers from DoD, DHS and FBI highlighted identity management interoperability as their key priority for 2010. Panelist included: Robert Mocny, Acting Director,…
EuroCloud Launches !!
Congratulations to Pierre-Jose Billotte for the successful launch of EuroCloud !! Established as a pan European network, EuroCloud are communities that represent a knowledgeable network of companies engaged local and…
Government Cloud Economics
In the The Economics of Cloud Computing, Gwen Morton and Ted Alford have published an EXCELLENT economic evaluation of the federal government’s push to cloud computing. Anyone interested in this…
Deputy CIA CIO Newest Ulitzer Author
Jill Tummler Singer, Deputy Chief Information Officer at the Central Intelligence Agency (CIA), is now a Ulitzer author. Appointed in November 2006, Ms Singer is responsible for ensuring CIA has…
Hybrid IT blends traditional datacenters, managed service providers, and cloud service providers to deliver the necessary mix of information technology services. This IT consumption model enables a composable infrastructure which describes a framework whose physical compute, storage, and network fabric resources are treated as services. Resources are logically pooled so that administrators no longer need to physically configure hardware to support a specific software application, which describes the function of a composable architecture.
Composable infrastructure architectures have two major functions. They must be able to disaggregate and aggregate resources into pools and compose consumable resources through a unified API. Overseeing these functions is management software that can also communicate with the API management functions.
From a management viewpoint, the use of composable architectures transforms the CIO and IT function into the collaboration and integration hub across all enterprise functions. This type of transformative infrastructure is foundational to contemporary agile business because a hybrid IT environment, private clouds, public clouds, community clouds, traditional data centers, and services from service providers must be integrated and interconnected.
The agility afforded by architecture composability lets applications and services be deployed to, and consumed from, the most appropriate service environment combination. When public clouds are used as an architecture component, enterprises are able to scale continuous delivery and innovation into product and service specifications.
From the infrastructure side, this modernization task transforms legacy data centers into private clouds and migrates existing legacy or packaged applications onto this highly automated environment.
This initial step toward establishing a hybrid cloud environment also enables a rational and collaborative adoption of public cloud infrastructure services (IaaS). It reduces the friction often caused by retraining staff in public cloud operations, modern infrastructure technologies, and composable solution management tools.
Composable infrastructures can build new revenue-generating products and services faster while simultaneously addressing the key inhibitors to change.
Composable infrastructures also enable the implementation of all IT software, infrastructure, and security features into production safely and quickly in a sustainable way. Broadly referred to as “continuous delivery,†this capability can significantly reduce the risk often associated with software deployments by establishing an operational environment within which updates and deployments can be performed on demand.
Multi-Access Edge Computing
Fifth-generation (5G) wireless networks will significantly enhance the current mobile network environment. These new networks will use multi-access edge computing (MEC) to extend composable enterprise infrastructures to the network edge, a capability broadly referred to as edge computing.
By using edge computing, content and applications can operate apart from their core data center in a disconnected manner. A similar concept, fog computing, describes an optional approach where the data is processed within a fog node or IoT gateway that is situated within the local area network.
This approach delivers services characterized by ultra-low latency and high bandwidth and real-time access to mobile network information. Composable enterprise infrastructures need to integrate and operate with geographically distributed compute and storage resources. To support this future IT-operating environment, enterprise content and application developers need to collaborate with telecommunications network operators to gain access to edge services. This allows more enterprise flexibility and speed in deploying innovative edge computing applications and services. Most modern applications are designed based on the distributed computing software development model.
For MEC, applications developers need to identify application features that require processing at the edge as distinct from features that need high compute power or that do not require near real-time response. Greengrass, for example, consists of the AWS Greengrass core for edge computing capabilities working with AWS IoT software development kit–enabled IoT devices.
Using this architecture, AWS IoT applications can respond in real time to local events and use cloud capabilities for all other data processing functions.
To deliver these new services and maximize the value of MEC, it is also important for the application developers and content providers to fully understand the core characteristics of the MEC environment and the distinguishing MEC services. A MEC point-of-presence (PoP) is different than a traditional cloud PoP and may offer significant advantages to edge applications and services.
Edge Computing Design
Edge computing application design development model has three locations:
- Client
- Near server
- Far server
An end-to-end IT service designed to operate in an IoT environment follows this model also but with different reference names or components:
- Terminal device component
- Edge component(s)
- Remote component(s)
The IoT architecture emphasizes the distribution of components.
Industry standards will help accelerate the application development for edge computing and MEC adoption. A MEC host contains a MEC platform and VMs or containers that hold the compute, storage, and network resources for edge applications. MEC offers a secure environment where applications may discover, advertise, consume, and offer services.
This assumption is not valid in edge computing and there are many IoT industry use cases where network aspects are integral to the application design. MEC application enablement introduces such a service environment and can be used to improve the user experience. An example would be doing preliminary processing in the edge device to determine the need for further action from core back-end services. This preliminary processing requires near-zero latency and needs the terminal device to support some computing capabilities.
While 5G networks will create many new opportunities, they also increase the risk to enterprise data. As this new network will be heavily dependent on software-defined–network (SDN) technologies, data may be more vulnerable to the compromise of confidentiality by the interception of data communications or unauthorized access to a universally available set of network services.
A software-defined network (SDN) is an information technology network that physically separates the network control plane from the data (or forwarding) plane in the data center. SDN uses network control plane software to enable dynamic, programmatically efficient network configuration in order to improve network performance and monitoring.
Replacing traditional dedicated hardware with a general-purpose computer and software is referred to as network function virtualization (NFV). In this environment, network services (i.e., routers, firewalls, load balancers, XML processing, and WAN optimization devices) are replaced with software running on virtual machines.
Key cybersecurity tasks include the following:
- Securing the controller as the centralized decision point for access to the SDN
- Protecting the controller against malware or attack
- Establish trust by protecting the communications throughout the network by ensuring the SDN controller, related applications, and managed devices are all trusted entities
- Creation of a robust policy framework that establishes a system of checks and balances across all SDN controllers
- Conducting forensics and remediation when an incident happens in order to determine the cause and prevent reoccurrence
If NFV is used, the SDN can also act as a hypervisor for NFV virtual machines.
Both technologies depend heavily on virtualization to enable network design and infrastructure to be abstracted in software and then implemented by underlying software across hardware platforms and devices. Approaches for implementing cybersecurity protections include:
- Embed security within the virtualized network devices
- Embed security into the SDN servers, storage, and other computing devices
NFV establishes a virtualized networking environment dedicated to providing different network services. SDN is a new form of threat because the centralized software controller manages all network flows.
Zero-Trust
This approach will not be efficient in 5G environments that require end-to-end security to serve new forms of specialized networks. To support this, a new trust model for 5G networks with an additional element of services compared to the traditional 4G trust model is required. With cloud, most of the data will be logically “outside†and in multiple systems in multiple locations, the zero-trust security model a necessity for the modern business.
The Zero Trust approach uses existing technologies and governance processes in securing the enterprise IT environment. It calls for the use of micro-segmentation and more granular perimeter enforcement based on users, their location, and additional data to determine whether to trust an entity seeking access to an enterprise asset.
When designing and deploying transformational solutions across enterprise, cloud and 5G networks, and MEC environment, the Zero Trust paradigm must be extended to include all associated software-defined networks (SDN). By combining the impact of these three capabilities within a new Zero Trust network model, companies can successfully build and deploy more flexible, more efficient, and more secure ecosystems.
The most critical challenges associated with operating these mixed infrastructure environments include the need for the following:
- New enterprise budgeting processes
- New technical baseline and procedures
- New IT service procurement processes
- Development of new products and services
- Establishing consensus around different organizational targets and goals
- Funding of training and education resources to acquire newly required skill sets
- Structural organization modifications All these challenges require executive backing and organizational process changes.
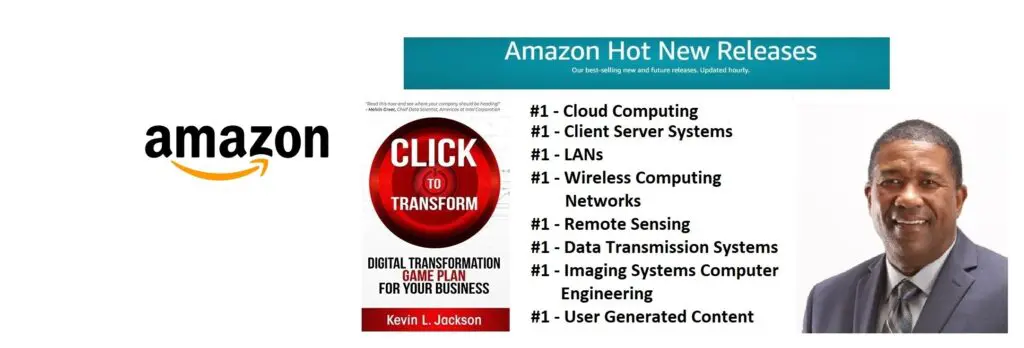
Would you like to learn more about digital transformation innovation? Pick up a copy of my new book, Click to Transform!Â
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
