Twitter Feed
SourceConnecte! Marketplace With A Mission
Earlier this year, GC GlobalNet launched a new breed of B2B e-commerce sites. Curated by Kevin L. Jackson, SourceConnecte (with an “eâ€) went live with three strategic goals in mind: Efficiently leverage modern…
Potential vs. Reality: Is Edge Computing Real?
Edge computing provides compute, storage, and networking resources close to devices generating traffic. Its benefits are based on an ability to provide new services capable of meeting stringent operational requirements…
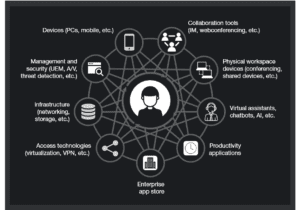
Enabling Digital Transformation
Digital transformation integrates technology into all areas of an organization’s business or mission. Its fundamental purpose is to create and deliver innovative and industry-changing products and services to a global…
The ThinkShield Story Part 1: The Challenge
The cybersecurity challenge seems to be growing daily. Threats are becoming more sophisticated, and attacks are becoming more destructive while the corporate world’s response seems to resemble a deer…
CIO dream team: Who’s in and why?
Today’s CIO navigates the twin challenges of enabling new business models and managing rapid technological change. Cloud computing strategies are now table stakes. CIOs must make complex decisions about using…
Digital Transformation and the Mainframe
Digital transformation infuses digital technology into all areas of an organization’s business or mission. Its fundamental purpose is to create and deliver innovative and industry-changing digital products and services to…
Composable Architecture Q&A. Are you ready?
Q: Is it time for my company to jump on the composable architecture bandwagon? A: Composable architectures are quickly becoming essential to the modern enterprise. Citing a recent Forrester study:…
Increase Productivity by Reducing Technology Distraction: Lessons from Forrester Research
Workplace productivity is hurt every day by the very technology developed and purchased to improve it. Forrester announced this surprising conclusion in their latest “How To Wake Up From The Nightmare…
Unveiling the end-to-end capabilities for the networked society
An Interview with Henrik Basilier By Kevin L. Jackson The telecom industry is rapidly moving towards a future in which networks must have the capabilities of delivering services with the…
AT&T Finance Solutions GM on Shrimping, Software, and CX
Helping clients address the trends and challenges presented by the Financial Services industry is the main focus for René Dufrene in his role as General Manager of Finance Solutions at…
- Public cloud is more easily breached that a private cloud
- Any infrastructure that you manage or own is more secure than any cloud computing infrastructure
- Cloud-hosted applications are technically no different than enterprise-hosted applications
- The cloud service provider infrastructure and personnel will address and remediate all security issues
- The end user has very little control over cloud security
- A corporate network provides protection even when using cloud apps
- Cloud platforms lack security features and cloud providers offer no visibility into their platform
- Strong authentication mechanisms are sufficient for ensuring security
Although every one of these statements have been proven false, they continue to be socially propagated. While this is sometimes done for self-serving commercial reasons, perpetrators are often well-meaning individuals holding critical corporate responsibilities. This latter scenario has been driven by the lack of industry consensus on security and a dearth of nonvendor specific cloud security training and certifications. Because cloud computing is a young industry so this is understandable, but maintaining this view exacerbates the harm.
These troubling facts are why I was thrilled last month when cloud computing security industry leaders Cloud Security Alliance (CSA) and the International Information System Security Certification Consortium ((ISC)²) addressed this issue head-on by collaborating on the development and release of the Certified Cloud Security Professional (CCSP) Certification Program. Both nonprofits, their individual missions and goals are synergistic:
CSA: To promote best practices for providing security assurance within cloud computing and provide education on the uses of cloud computing to help secure all other forms of computing.
(ISC)²: To support and provide members and constituents with credentials, resources, and leadership to secure information and deliver value to society.
By stepping up to the challenge of cloud security certification, these organizations are explicitly addressing their missions.
Vendors are also stepping up. According to a recent CRN article, commercial cloud security platforms are helping enterprises mitigate the risks of using cloud-based applications and services. These offering are providing strong data protection capabilities by incorporating data loss prevention, data encryption and tokenization. Some cloud security companies provide identity and access
management capabilities while others monitor cloud-based systems for suspicious activity and provide policy enforcement, reporting and alerting capabilities. Cloud-based sandbox environments for controlling employee laptops, smartphones and tablets, regardless of their location, are in the marketplace as well.
A specific example of strong industry cloud security capabilities is Dell SecureWorks. It is positioned in the Leader’s Quadrant of Gartner’s Magic Quadrant for Global Managed Security Service Providers. In April 2015, the Info Security Products Guide recognized the company by announcing Dell as the Grand Trophy Winner as well as the winner of 12 additional awards, including one in cloud security for the Dell Cloud Access Manager.
The CCSP credential was designed to reflect the holder’s deep knowledge of cloud computing security. In order to gain this certification, a candidate must demonstrate hands-on information security and cloud computing experience. Certification requires a minimum of five years of cumulative, paid, full-time information technology experience, of which three years must be in information security and one year in one of six domains of the CCSP examination. It also requires:
- Passing an exam;
- A legal commitment to the code of ethics;
- Endorsement from an appropriate certified professional; and a
- Commitment to continuing professional education.
In providing the CCSP certification, CSA and (ISC)² have set a new benchmark for cloud security knowledge and competence. They have also established a reliable indicator for overall proficiency in cloud security and have gone a long way toward eliminating cloud computing security misconceptions and misunderstandings.
This post was written as part of the Dell Insight Partners program, which provides news and analysis about the evolving world of tech. Dell sponsored this article, but the opinions are my own and don’t necessarily represent Dell’s positions or strategies.
( Thank you. If you enjoyed this article, get free updates by email or RSS – © Copyright Kevin L. Jackson 2015)
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes