Twitter Feed
Vivek Kundra to Speak at NRO Showcase
On the 17 & 18 June, the National Reconnaissance Office (NRO) will present the premiere Innovative Solutions Showcase. Titled “Unleashing the Crowd in the Cloud: Igniting the Innovation Insurgency“, this event…
Secure Cloud Computing on Federal News Radio
Last week the Trezza Media Group, Flyzik Group and Federal News Radio combined to produce an outstanding Federal Executive Forum on Secure Cloud Computing. Moderated by Jim Flyzik, panelist included:…
My Meeting with Mr. Vivek Kundra
Earlier this week I had the distinct pleasure and opportunity to have a private meeting with Mr. Vivek Kundra. Although my time with him and Mr. Gary Washington (OMB/Egov &IT Internal…
Comments for Mr. Kundra (Thank you for the input!)
A little over a week ago I put out a request to my readers to help me with my meeting with Vivek Kundra. The response has been awesome!! thank you…
Congratulations to Roger Baker !!
My congratulations goes out to Roger Baker ! I first met Roger a little over a year ago when he interviewed me for my present job at Dataline. At that…
NDU (IRM) and DoD CIO (NII) Co-Hosting Cloud Computing and Cyber Security Symposia
I’m proud to announce two important coming events. The Information Resources Management (IRM) College and the Office of the Assistant Secretary of Defense (Networks and Information Integration)/DOD CIO are co-hosting…
Please Help Me Plan My Meeting With Mr. Vivek Kundra !!
A couple of weeks ago, I was offered a chance to meet Mr. Vivek Kundra at the Eisenhower Executive Office Building in downtown Washington, DC. Needless to say, I was…
President Obama’s 2010 Budget Highlights Cloud Computing
President Obama’s 2010 Budget (pp. 157-158) has highlighted cloud computing as a key tool for improving innovation, efficiency and effectiveness in Federal IT. ” Cloud-computing is a convenient, on-demand model…
Federal Cloud Computing Heating Up !
As fellow blogger Reuven Cohen mentions in his post, Federal cloud computing is indeed heating up: Vivek Kundra held a US Federal Government Cloud Computing Summit yesterday The Federal CIO…
USA.gov “Flips the switch” to Cloud Computing
Last weekend, USA.gov shifted to a cloud computing platform. This move is expected to reduce infrastructure expenses by 90% and drastically improve flexibility. “‘We are flipping the switch tomorrow to…
Today data has replaced money as the global currency for trade.
“McKinsey estimates that about 75 percent of the value added by data flows on the Internet accrues to “traditional” industries, especially via increases in global growth, productivity, and employment. Furthermore, the United Nations Conference on Trade and Development (UNCTAD) estimates that about 50 percent of all traded services are enabled by the technology sector, including by cross-border data flows.”
As the global economy has become fully dependent on the transformative nature of electronic data exchange, its participants have also become more protective of data’s inherent value. The rise of this data protectionism is now so acute that it threatens to restrict the flow of data across national borders. Data-residency requirements, widely used to buffer domestic technology providers from international competition, also tends to introduce delays, cost and limitations to the exchange of commerce in nearly every business sector. This impact is widespread because it is also driving:
- Laws and policies that further limit the international exchange of data;
- Regulatory guidelines and restrictions that limit the use and scope of data collection; and
- Data security controls that route and allow access to data based on user role, location and access device.
A direct consequence of these changes is that the entire business enterprise spectrum is now faced with the challenge of how to classify and label this vital commerce component.
 |
|
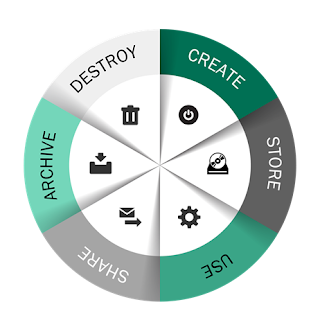
Figure 1– The data lifecycle
|
The challenges posed here are immense. Not only is there an extremely large amount of data being created everyday but businesses still need to manage and leverage their huge store of old data. This stored wealth is not static because every bit of data possesses a lifecycle through which it must be monitored, modified, shared, stored and eventually destroyed. The growing adoption and use of cloud computing technologies layers even more complexity to this mosaic. Another widely unappreciated reality being highlighted in boardrooms everywhere is how these changes are affecting business risk and internal information technology governance. Broadly lumped into cybersecurity, the sparsity of legal precedent in this domain is coupled almost daily with a need for headline driven, rapid fire business decisions.
To deal with this new reality, enterprises must standardize and optimize the complexity associated with managing data. Success in this task mandates a renewed focus on data classification, data labeling and data loss prevention. Although these data security precautions have historically been
glossed over as too expensive or too hard, the penalties and long term pain associated with a data breach incident has raised the stakes considerably. According the Global Commission on Internet Governance, the average financial cost of a single data breach could exceed $12,000,000 [1] , which includes:
- Organizational costs: $6,233,941
- Detection and Escalation Costs: $372,272
- Response Costs: $1,511,804
- Lost Business Costs: $3,827,732
- Victim Notification Cost: $523,965
So is adequate data classification still just simply a bridge too far?
While the competencies required to implement an effective data management program are significant, they are not impossible. Relevant skillsets are, in fact, foundational to the deployment of modern business automation which, in turn, represents the only economical path towards streamlining repeatable processes and reducing manual tasks. Minimum steps include:
- Improving enterprise awareness around the importance of data classification
- Abandoning outdated or realistic classification schemes in order to adopt less complex ones
- Clarifying organizational roles and responsibilities while simultaneously removing those that have been tailored to individuals
- Focus on identifying and classifying data, not data sets.
- Adopt and implement a dynamic classification model.[2]
The modern enterprise must either build these competencies in-house or work with a trusted third party to move through these steps. Since the importance of data will only increase, the task of implementing a modern data classification and modeling program is destined to become even more business critical.
( This post was brought to you by IBM Global Technology Services. For more content like this, visit Point B and Beyond.)
[2] Recommended steps adapted from “Rethinking Data Discovery And Data Classification by Heidi Shey and John Kindervag, October 1, 2014, available from IBM at https://www-01.ibm.com/common/ssi/cgi-bin/ssialias?htmlfid=WVL12363USEN
( Thank you. If you enjoyed this article, get free updates by email or RSS – © Copyright Kevin L. Jackson 2015)
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes


