Twitter Feed
Mobile device security: A new frontier for hackers
Recent security breaches have heightened our awareness of cybersecurity issues. The hack and other security breaches have resulted in unprecedented damages. However, the majority of mobile device users have yet to be sensitized…
Learn How To Buy Cloud From GovLoop & ViON
“Government IT managers must accept that cloud computing services are services, not the purchases of technology. This usually represents a fundamental change in how technology is acquired and managed. Since…
A VETS 360 BENEFIT – LATINO FILM INDUSTRY POST OSCAR PARTY
GUESS WHO SUPPORTS VETS 360? You can support them too at the: THE OFFICIAL LATINO FILM INDUSTRY POST OSCAR PARTY The Veterans 360 mission is to support our young combat…
South Asia’s Biggest Tech Event – “Digital World 2015”
I am proud and honored to announce that I have been added as a speaker at SouthAsia’s biggest tech event “Digital World 2015” , 9th – 12th February, 2015 at…
Fear Hackers? First invest in an IT security culture change
by Kevin L.Jackson With all the news these days about cyberterrorism and hacking the cloud may seem like the last place you would want to put your precious information. Pew…
CloudCamp Bangladesh In Dhaka! – February 11, 2015
Did you know that….. Goldman Sachs recognized Bangladesh as one of the Next Eleven (N-11) – a list of eleven countries having strong potential for becoming the world’s largest economies…
Agile is not the absence of ITIL!
by Jodi Kohut ITIL (formerlyknown as the Information Technology Infrastructure Library) has been the best management practices framework of choice for world class IT Operations organizations. The 5 stage framework:…
Cloud Security: Understanding the Cloud Computing Threat Landscape
In the last two years, IT security breaches have hit the White House, the State Department, the top federal intelligence agency, the largest American bank, the top hospital operator, energy…
Federal Cloud Computing Summit on January 14-15, Washington, DC
The Federal Cloud Computing Summit will be held on January 14-15, 2015 at the Marriott Metro Center in Washington, D.C. (Complimentary government and academic registration) This educational symposium will feature cloud computing…
CONGRATULATIONS! Inaugural Cloud Computing Class at Mira Costa College Graduates!!
Anthony Dorrah, Jose Chapman, Mike Chatelain, Lisa Heiden, Ginelle Johnson, Robert Minson, Alfredo Morales We are so proud of the success of out first cloud computing training class. This group…
It’s amazing what a little radio time will do!
Since Sunday’s broadcast, I’ve been asked numerous times about my real answer to the question “Will ‘Cloud Computing’ Work In White House“. Although I would never assume to be in a position to advise the President-elect, I’m more than happy, however, to add my voice to the Center for Strategic and International Studies (CSIS) and the distinguished list of contributors that recently released the CSIS Commission on Cybersecurity for the 44th Presidency.
I truly believe that cloud computing technology can be used to implement some of their recommendations. One in particular is their recommendation for a National Office for Cyberspace (NOC) and a new National Security Council Cybersecurity Directorate (NSCCD). Along with the relevant agencies, these organizations would:
“Assume expanded authorities, including revised Federal Information Security management Act (FISMA) authorities, oversight of the Trusted Internet Connections (TIC) initiative, responsibility for the Federal Desktop Core Configuration (FDCC) and acquisition reform, and the ability to require agencies to submit budget proposals relating to cyberspace to receive its approval prior to submission to OMB.”
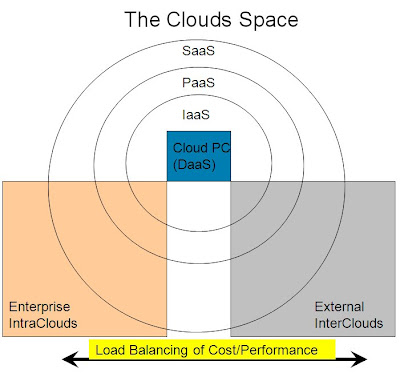
As widely discussed in cloud computing circles, Infrastructure-as-a-service (IaaS), platform-as-a-service (PaaS) and software-as-a-service (SaaS) are all the required components for desktop-as-a-service (DaaS). If applied to a private government cloud, this approach could be easily adopted for the Federal Desktop Core Configuration (FDCC). (Thanks goes to Avner Algom of the Israeli Association of Grid Technologies for this insightful graphic)
As I discussed on the NPR program, cryptographic data splitting could also aid in the management and protection of information in the cloud. As proposed in the CSIS report, the NOC and NSCCD would:
“Manage both a new federated regulatory approach for critical cyber infrastructure and a collaborative cybersecurity network across the federal government”
This would be akin to a “Federated Service Oriented Architecture” where a governance and security layer would be used to simultaneously improve cross-agency collaboration and inter-agency security. Couldn’t this actually be the basis for a governmental private cloud? By developing and implementing appropriate standards and protocols for the government-wide, federated SOA layer, the NOC and NSCCD could quickly implement the suggested federated regulatory approach.
As emphasised repeatedly in the CSIS report, cyberspace is a vital asset for the nation. International engagement in order to establish international norms for cyberspace security is also stressed. What better way to set these international norms than to work diligently toward establishing a global, interoperable, secure cloud computing infrastructure.
3 Comments
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes

I more than agree with the ideas raised by Kevin.
As part of the work done by IGT (the Israeli Association of Grid Technologies) in the last 3 years – we are aiming to create a grid based Enterprise Service Bus, as a foundation for federated SOA – which we now can see an innovative usage for it.
Very refreshing observation of Kevin on the way SOA and Cloud emerge together.
Thanks Ronen. I think that a federated SOA may be an excellent pathway for transitioning to a private cloud.
^^Thanks!!
徵徵徵婚前徵信徵婚姻感情徵大陸抓姦徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵外遇抓姦法律諮詢家暴徵婚前徵信尋人感情挽回大陸抓姦離婚徵徵工商徵信徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵婚前徵信外遇抓姦感情挽回尋人大陸抓姦離婚家暴徵徵工商徵信法律諮詢徵徵徵跟蹤徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵工商徵信徵徵婚前徵信感情挽回外遇抓姦法律諮詢家暴尋人大陸抓姦離婚徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵大陸抓姦徵外遇徵徵徵尋人徵徵家暴徵徵徵徵徵徵徵徵徵工商徵信法律諮詢家暴感情挽回大陸抓姦外遇婚前徵信離婚徵徵尋人徵徵徵徵徵徵徵徵徵徵徵徵工商徵信徵徵徵徵徵徵外遇抓姦法律諮詢家暴婚前徵信大陸抓姦尋人感情挽回徵徵徵徵徵徵徵徵徵徵外遇抓姦婚前徵信感情挽回尋人大陸抓姦工商徵信法律諮詢離婚家暴徵徵徵徵徵徵徵徵徵徵徵徵徵徵工商徵信外遇抓姦法律諮詢家暴婚前徵信尋人感情挽回大陸抓姦離婚徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵婚前徵信工商徵信外遇抓姦尋人離婚家暴大陸抓姦感情挽回法律諮詢徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵離婚感情挽回婚前徵信外遇抓姦家暴尋人徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵工商徵信外遇抓姦法律諮詢家暴婚前徵信尋人感情挽回">徵大陸抓姦離婚徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵婚前徵信工商徵信外遇抓姦尋人離婚家暴大陸抓姦感情挽回法律諮詢徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵徵