Twitter Feed
Transformation Network
The Achilles heel of every transformative business model is their reliance on ever increasing amounts of data that need to be transported quickly across wide area networks and processed at…
Essential Characteristics of Cloud Computing as Digital Transformation
Hybrid IT blends traditional datacenters, managed service providers, and cloud service providers to deliver the necessary mix of information technology services. This IT consumption model enables a composable infrastructure which…
Transformation Innovation
4 Factors Driving Digital Transformation ROI The critical assessment factors for cloud ROI risk probability are the following: Infrastructure utilization Speed of migration to cloud Ability to scale business/mission processes…
Transformation Frameworks
Digital transformation necessitates changes in an organization’s operational processes. According to Harvard, a focus on operations can lead to business process optimization and entirely new revenue streams. Three common routes…
Transformation Infrastructure
Hybrid IT enables a composable infrastructure which describes a framework whose physical compute, storage, and network fabric resources are treated as services. Resources are logically pooled so that administrators need…
Essential Characteristics of Cloud Computing as Digital Transformation
A survey of 2,000 executives conducted by Cognizant in 2016 identified the top five ways digital transformations generate value: Accelerating speed to market Strengthening competitive positioning Boosting revenue growth Raising…
Embrace Transformation
From a business perspective, differentiating business processes and quality customer service are central to overall success. Business leaders must therefore clearly identify and measure how information technology contributes to the…
Computer Vision Advances Zero-Defect Manufacturing
by Kevin L. Jackson Electronics manufacturers operate in a challenging environment. It’s hard enough to keep up with the ever-accelerating rate of change in the industry. Now customers want increasingly…
Real-Time Analytics Power the Roadway of the Future
By Kevin L. Jackson The complexities of citywide traffic are pushing the limits of existing transportation management systems. Outdated infrastructure is based on proprietary, single-purpose subsystems, making it costly to…
Thriving on the Edge: Developing CSP Edge Computing Strategy
Communications Service Providers (CSPs) are facing significant business model challenges. Referred to generally as edge computing, the possibilities introduced by the blending of 5G networks and distributed cloud computing technologies are…
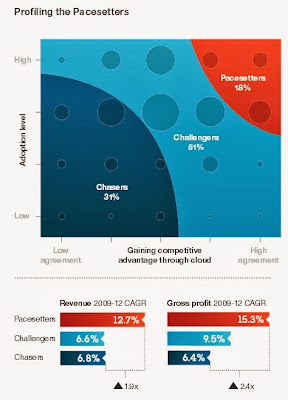
Industry’s transition from custom made, one-of-a-kind IT infrastructures to the standardize, commodity based cloud paradigm is well on it’s way. IBM’s recent “Under Cloud Cover” study highlights the rapidly of this global transformation:
users, business leaders of all stripes – Finance, Sales & Marketing, Product
Development and more – are becoming increasingly focused on the business value
cloud provides. Over the next three years, cloud’s strategic importance to business
users is expected to double from 34 percent to 72 percent, even surpassing their IT
counterparts at 58 percent.”
What seems surprising, however, is that this shift is happening even in the face of repeated cautions and warnings about the security of public clouds. The key challenge for decision makers is how to balance the business need to quickly transition to cloud with the equally important business need of maintaining information security and privacy.
Lucky for us, two recent public cloud reports from Gartner and Cloud Spectator have gone a long way toward addressing this critical question. Gartner’s “Toolkit: Comparison Matrix for Cloud Infrastructure as a Service Providers, 2013” provides a comparative scoring of the security and compliance capabilities of the Gartner Public IaaS Magic Quadrant companies while Cloud Spectator has recently provided a price/performance scoring for the same group of companies. I’ve used this data to produce the Price/Performance vs Security chart below.
 |
| Click to enlarge |
While this marketplace snapshot is definitely not definitive, this data should certainly help us all who are charged with managing this important transition.
( The Price-Performance score is a blend of technical performance obtained from Cloud Spectator and use case performance obtained from Gartner. In the chart, the higher the value on the vertical axis, the better. Security score was obtained from Gartner. The further to the right on the horizontal axis, the better. Since CSC was not included in Cloud Spectator’s performance analysis they are also not included in the chart provided above.)

( Thank you. If you enjoyed this article, get free updates by email or RSS – © Copyright Kevin L. Jackson 2012)
P
2 Comments
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes











Very interesting take on the two analyses, Kevin!
Just out of curiosity, which price/performance values did you use from the Cloud Spectator report? The system performance?
The information here is well-illustrated, and simplifies a range of concerns brought up in the cloud industry. Thanks for the post, and I look forward to seeing more information like this in the future.
Thanks. I just updated to post in order to clarify data origin. The Price-Performance score is a blend of technical performance (CloudSpec Score) obtained from Cloud Spectator and use case performance obtained from Gartner. I then normalized the values using equal weight. In the chart, the higher the value on the vertical axis, the better. Security score was obtained from Gartner. The further to the right on the horizontal axis, the better.