Twitter Feed
Enomaly: Startup of the Week
Congratulations to Enomaly and Reuven Cohen for being named Startup of the Week byInformationWeek !!! Reuven and I collaborate quite a bit and his blog, Elastic Vapor, is a staple for anyone interested in…
Cloud Computing at DoD, DISA, DIA, CENTCOM and NCOIC
At CloudCamp last week, Military Information Technology distributed free copies of it’s November issue to all attendees. The issue contains a very informative article by Cheryl Gerber titled “Computing in…
Last Night’s Camp Out !!
Check out Tech BISNOW for more on CloudCamp Federal! Follow me at https://Twitter.com/Kevin_Jackson
CloudCamp Federal was AWESOME !!
Just got home from CloudCamp Federal. What an event!! The over 100 attendees definitely made the statement that the Fed is interested in cloud computing. As expected, cloud security was…
DISA taps CollabNet to manage DoD cloud software development
This week, the Defense information Systems Agency (DISA) announced that they will be using Collabnet tools to manage application development for RACE. The Computerworld article said that DISA will use…
Today is CloudCamp Federal !!
Today we kick of off the first CloudCamp Federal. Reuven Cohen, Bob Lozano, Brand Niemann and over 150 other cloud computing enthusiast are expected to attend. We also plan to…
CloudCamp “Sold Out” !! More Tickets Added
We are happy to announce that CloudCamp Federal (aka DC), taking place tomorrow at Apptis headquarters in Chantilly, VA (directions), is sold out. But don’t fret, we’ve added 25 more…
Only 9 tickets left for CloudCamp Federal !!
Only 9 tickets left from the original allotment of 150 for CloudCamp Federal this week. We’re working to free up some more, but don’t leave it to chance. Go to…
Valiant Angel – A Perfect PED Application for Cloud Computing
A few weeks ago in an article title “Why the Cloud? Processing, Exploitation and Dissemination“, I described two instances where the newspaper industry used cloud computing in order to process,…
 |
| Photo credit: Shutterstock |
With all the excellent training available on television today, we are all now well prepared to deal with the coming Zombie Apocalypse. Our failure as a society lies, however, in our misunderstanding of the nature of the cybersecurity challenge. This failure threatens us all and our survival will depend on society’s ability to deal with the evolution and maturation of the changing enterprise cybersecurity challenge.
If you’re completely oblivious to the living dead threat, a zombie apocalypse refers to a widespread (usually global) rise of zombies hostile to human life. The zombies will engage in a general assault on civilization where victims may become zombies themselves. This causes the outbreak to become an exponentially growing crisis. The spreading phenomenon swamps normal military and law
enforcement organizations, leading to the panicked collapse of civilized society until only isolated pockets of survivors remain, scavenging for food and supplies in a world reduced to a pre-industrial hostile wilderness.
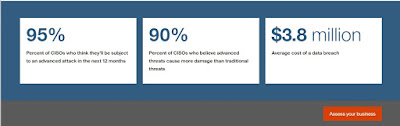
A recent report from the Herjavec Group describes the coming Hackerpocalypse as a similar global assault on modern society. The reports description puts the nature of global cybercrime in perspective by highlighting that:
- Annual costs attributable to cybercrime are expected to rise from $400B in 2015 to more than $6T by 2021;
- From 2012 to 2017, enterprise cumulative spend on cybercrime defense will exceed $1T. Some say that even if this estimate includes data collection, storage, security, analysis, threat intelligence operations and dissemination it still barely scratches the surface;
- Black-Hat hackers, motivated by money, espionage, notoriety, and malicious intent, become even more nimble, experienced and daring than their White Hats adversaries who are constrained by boundaries and rules;
- Continuing lack of effective cybercrime law enforcement
- A severe cybersecurity workforce shortage of 1 million cybersecurity in 2016, will reach 1.5 million by 2019;
- Hybrid warfare, a new type of global conflict where conventional and cyber warfare are combined and in which the aggressor avoids attribution or retribution, is now front page news.
Please don’t be lulled by an apparent separation between the virtual cyber world and our “real-life” physical one. An economic cyberattack could mortally disable the economy of a city, state or country, according to a recent RSA Conference blog post . Ted Koppel also revealed in a New York Times investigative piece that a major cyberattack on the United States’ electrical power grid is likely and that it would be devastating. A national cyberattack against power grids in Ukraine, not only crippled that county’s power systems but mining and railway companies as well.
To prepare for this almost inevitable battle, enterprise cyber defense teams must focus on an actionable list of “to do’s” which include the basics like:
- Developing a practical plan to manage devices, end-user applications and related network infrastructure;
- Designing, implementing and managing an integrated communications and networking environment;
- Updating and regularly testing your business continuity processes to enable recovery of critical business applications no matter the circumstances;
- Building and managing an efficient infrastructure with the ability to respond to change and drive innovation; and
- Simplifying management and streamlining maintenance of your multi-vendor IT supply chain.
Standalone controls will not work against the sophisticated Hackerpocalypse menace. Once implanted, these advanced threats can remain hidden for months, or even years, collecting critical information and inflicting serious damage. Enterprises must adopt a multi-layered approach that leverages next-generation defenses with embedded intelligence and analytics.
( This post was brought to you by IBM Global Technology Services. For more content like this, visit Point B and Beyond.)
.
( Thank you. If you enjoyed this article, get free updates by email or RSS – © Copyright Kevin L. Jackson 2015)
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes