Twitter Feed
Cloud Computing Price-Performance Could Vary By 1000%!
by Kevin L. Jackson Yes, you read that right. The price/performance of your cloud computing infrastructure could vary as much as 1000 percent depending on time and location. High levels of…
E-book: Educate Yourself With Dell Insight Partner Views on Cybersecurity
Data security breaches and hacker attacks on private businesses, health organizations and government agencies in the U.S. have grabbed headlines with increasing frequency, it seems. There is zero doubt about…
IEEE Cloud Computing Magazine Focuses On GovCloud
Today I am especially proud and honored to publicly announce my appointment to the IEEE Cloud Computing Magazine Editorial Board! I am truly appreciative to Dr. Alan Sill and Dr.…
Is Social Media Right For Your Small Business?
Everyone from pre-teens to granddads, does social media today. With Twitter, Instagram, Facebook and many newer ways to stay in the know popping up every day, picking the right platform…
Rob Davies, ViON SVP, Talks about Government Cloud Computing
ViON solves complex enterprise problems by combining passion and agility to deliver the most effective, innovative solutions because commitment to mission success is in their DNA. One of the ways…
New Approaches for New Big Data Insights
by Melvin Greer Business Intelligence has matured as a core competency necessary to sustain competitive advantage. Organizations of every size and industry are generating valuable data with each interaction, and…
How to Put Public Sector Data Migration Hassles on the Road to Extinction
With careful planning and the right technology, Federal, State and Local Government IT Leaders can overcome fears of data migrations, breaking free from archaic procedures to lead the pack By…
Would you build your house from a Visio diagram?
Would you even hire an architect that highlighted hand drawn diagrams and spreadsheets as their design tools of choice? Of course you wouldn’t. Not using computing aided design (CAD) as…
Industry leaders set cloud computing security benchmarks
Security has long been the No. 1 cloud computing business concern. Although the apprehension is absolutely valid, cloud computing business decision and strategies are all too often driven by the…
The Science and Art of Business Leadership
Business leadership is both science and art. The scientific aspects revolve around finance, organization, products and service. Artistic aspects include relationships, market trajectories and business strategies. While many focus on…
Hybrid IT enables a composable infrastructure which describes a framework whose physical compute, storage, and network fabric resources are treated as services.
Resources are logically pooled so that administrators need to physically configure hardware to support a specific software application, which describes the function of a composable architecture.
This type of transformative infrastructure is foundational to contemporary agile business because a hybrid IT environment, private clouds, public clouds, community clouds, traditional data centers, and services from service providers must be integrated and interconnected.
Composable infrastructures can build new revenue-generating products and services faster while simultaneously addressing the key inhibitors to change, which include the following:
- General concerns regarding lack of adequate hybrid infrastructure security
- The false impression that cloud cannot support the operational/performance requirements of critical applications (e.g., SAP and Oracle)
- Management challenge presented by multi-cloud environments contracts that will include varying levels of governance and service-level agreements (SLAs)
- The need to match employee management skills across various cloud platforms
Composable infrastructure architectures have two major functions. They must be able to disaggregate
and aggregate resources into pools and compose consumable resources through a unified API.
Fifth-generation (5G) wireless networks will significantly enhance the current mobile network environment. These new networks will use multi-access edge computing (MEC) to extend composable enterprise infrastructures to the network edge, a capability broadly referred to as edge computing.
To support this future IT-operating environment, enterprise content and application developers need to collaborate with telecommunications network operators to gain access to edge services.
Using this architecture, “Internet of Things†(IoT) applications can respond in real time to local events and use cloud capabilities for all other data processing functions.
Edge computing application design development model has three locations:
- Client
- Near server
- Far server
An end-to-end IT service designed to operate in an IoT environment follows this model also but with different reference names or components:
- Terminal device component
- Edge component(s)
- Remote component(s)
The IoT architecture emphasizes the distribution of components. In this environment, network services (i.e., routers, firewalls, load balancers, XML processing, and WAN optimization devices) are replaced with software running on virtual machines.
To ensure secure operations, key cybersecurity tasks include the following:
- Securing the controller as the centralized decision point for access to the Software Defined Network (SDN)
- Protecting the controller against malware or attack
- Establish trust by protecting the communications throughout the network by ensuring the SDN controller, related applications, and managed devices are all trusted entities
- Creation of a robust policy framework that establishes a system of checks and balances across all SDN controllers
- Conducting forensics and remediation when an incident happens in order to determine the cause and prevent reoccurrence
Network Function Virtualization (NFV) establishes a virtualized networking environment dedicated to providing different network services. If NFV is used, the SDN can also act as a hypervisor for NFV virtual machines.
Approaches for implementing cybersecurity protections include the following:
- Embed security within the virtualized network devices
- Embed security into the SDN servers, storage, and other computing devices
The Zero Trust security model is centered on the belief that organizations should not trust anything inside or outside their perimeters. This model requires verification of anything and everything trying to connect to its systems before access is granted. The Zero Trust approach uses existing technologies and governance processes in securing the enterprise IT environment.
When designing and deploying transformational solutions across enterprise, cloud, 5G networks, MEC environment, and the Zero Trust paradigm must be extended to include all associated SDNs.
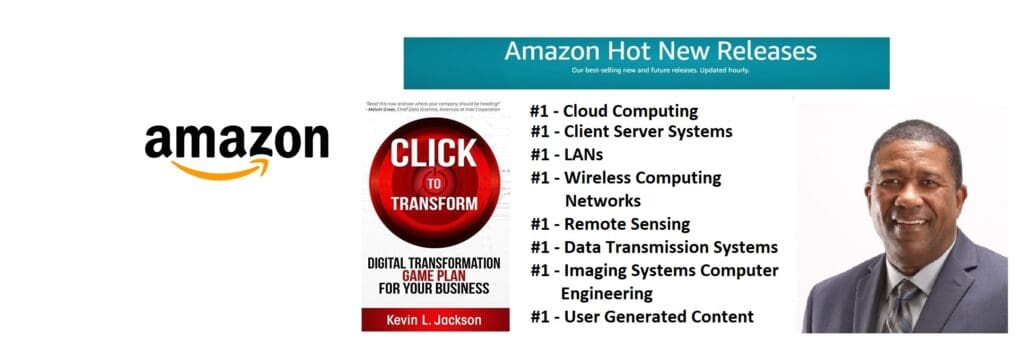
Read more about digital transformation and transformation infrastructure: grab a copy of my new book, Click to Transform, out today!
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
