Twitter Feed
Mr. Jeffrey Kaplan Talks About The Cloud Channel
This afternoon I had a very interesting discussion with Mr. Jeffrey Kaplan, Managing Director of THINKstrategies and founder of the Cloud Computing Showplace. His firm is focused entirely on the…
The Economic Benefit of Cloud Computing
(The following is the Executive Summary of a recent NJVC Executive Whitepaper. The full version is available at NJVC.com ) Cloud computing, as defined by the National Institute of Standards…
Implementation of Cloud Computing Solutions in Federal Agencies: Part 4 – Cloud Computing for Defense and Intelligence
(This is part 4 of the series entitled “Implementation of Cloud Computing Solutions in Federal Agencies”. First published on Forbes.com, this series provides the content of a whitepaper I recently…
Implementation of Cloud Computing Solutions in Federal Agencies : Part 3 – Cloud Transition Lessons Learned
(This is part 3 of the series entitled “Implementation of Cloud Computing Solutions in Federal Agencies”. First published on Forbes.com, this series provides the content of a whitepaper I recently…
FedPlatform.org Focuses on a Government PaaS
With GSA now issuing ATOs and Amazon launching it’s own government specific cloud, IaaS for government agencies is now a reality. This next step in this “Cloud First” march…
On The Frontlines: GovCloud and Cybersecurity
My friends at Trezza Media recently published a couple of great online documents on GovCloud and Cyber. Your should especially check out the “Cloud Chopping Made Easy” by David McClure…
GovCloud Is Now For Real !!
On Friday July 1, Infrastructure-as-a-Services for the US federal government became a reality with Authority to Operate (ATO) approval for the following vendors: Web Hosting CGI Federal Computer Literacy World…
The Economic Impact of GovCloud
What a month! June has really been busy!! Just now getting around to doing a post about CloudExpo 2011 in New York.With over 5000 delegates in attendance, it was just…
Hybrid IT enables a composable infrastructure which describes a framework whose physical compute, storage, and network fabric resources are treated as services.
Resources are logically pooled so that administrators need to physically configure hardware to support a specific software application, which describes the function of a composable architecture.
This type of transformative infrastructure is foundational to contemporary agile business because a hybrid IT environment, private clouds, public clouds, community clouds, traditional data centers, and services from service providers must be integrated and interconnected.
Composable infrastructures can build new revenue-generating products and services faster while simultaneously addressing the key inhibitors to change, which include the following:
- General concerns regarding lack of adequate hybrid infrastructure security
- The false impression that cloud cannot support the operational/performance requirements of critical applications (e.g., SAP and Oracle)
- Management challenge presented by multi-cloud environments contracts that will include varying levels of governance and service-level agreements (SLAs)
- The need to match employee management skills across various cloud platforms
Composable infrastructure architectures have two major functions. They must be able to disaggregate
and aggregate resources into pools and compose consumable resources through a unified API.
Fifth-generation (5G) wireless networks will significantly enhance the current mobile network environment. These new networks will use multi-access edge computing (MEC) to extend composable enterprise infrastructures to the network edge, a capability broadly referred to as edge computing.
To support this future IT-operating environment, enterprise content and application developers need to collaborate with telecommunications network operators to gain access to edge services.
Using this architecture, “Internet of Things†(IoT) applications can respond in real time to local events and use cloud capabilities for all other data processing functions.
Edge computing application design development model has three locations:
- Client
- Near server
- Far server
An end-to-end IT service designed to operate in an IoT environment follows this model also but with different reference names or components:
- Terminal device component
- Edge component(s)
- Remote component(s)
The IoT architecture emphasizes the distribution of components. In this environment, network services (i.e., routers, firewalls, load balancers, XML processing, and WAN optimization devices) are replaced with software running on virtual machines.
To ensure secure operations, key cybersecurity tasks include the following:
- Securing the controller as the centralized decision point for access to the Software Defined Network (SDN)
- Protecting the controller against malware or attack
- Establish trust by protecting the communications throughout the network by ensuring the SDN controller, related applications, and managed devices are all trusted entities
- Creation of a robust policy framework that establishes a system of checks and balances across all SDN controllers
- Conducting forensics and remediation when an incident happens in order to determine the cause and prevent reoccurrence
Network Function Virtualization (NFV) establishes a virtualized networking environment dedicated to providing different network services. If NFV is used, the SDN can also act as a hypervisor for NFV virtual machines.
Approaches for implementing cybersecurity protections include the following:
- Embed security within the virtualized network devices
- Embed security into the SDN servers, storage, and other computing devices
The Zero Trust security model is centered on the belief that organizations should not trust anything inside or outside their perimeters. This model requires verification of anything and everything trying to connect to its systems before access is granted. The Zero Trust approach uses existing technologies and governance processes in securing the enterprise IT environment.
When designing and deploying transformational solutions across enterprise, cloud, 5G networks, MEC environment, and the Zero Trust paradigm must be extended to include all associated SDNs.
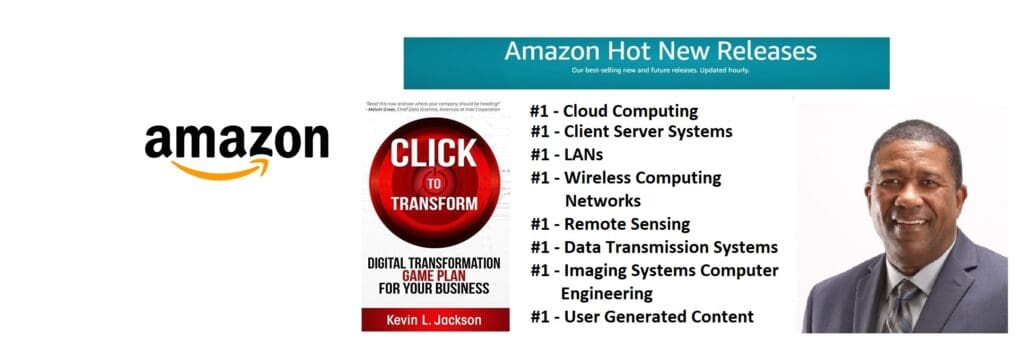
Read more about digital transformation and transformation infrastructure: grab a copy of my new book, Click to Transform, out today!
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
