Twitter Feed
Watson Crowdsources Cloud Computing
Recently I’ve been doing quite a bit of analysis work using the IBM Watson cognitive business platform. The really exciting thing about this opportunity is the way data can seem…
New Horizons® Delivers CloudMASTER®
For over 30 years, New Horizons has provided more than 30 million students with industry-leading technical training that delivers the most relevant and intuitive computer courses and certifications. They are…
See You At RSA Conference 2017!
JUST ANNOUNCED!! I am personally excited to be delivering the (ISC)² CCSP Two-Day Crash Course at RSA Conference 2017! “The current state of cybersecurity means there are many opportunities for the…
#KnowYourData: The Key to Business
Last week’s Strata-Hadoop conference in New York, NY was showcase of how big data is redefining business. Every company, every demonstration and every conversation highlighted how data is driving the…
A New Chapter: “Cloud Musings en español”
Since May 2010, “Cloud Musings” has demonstrated, educated and celebrated the use of advanced technology in business. Specific subjects are sometimes varied, but cloud computing and cybersecurity seem to have…
Military Tips On Business Resiliency
Photo credit: Shutterstock A steel bar is resistant to stress and is capable of maintaining its form while bearing large loads. While steel is also known as one of the…
Meet Ameet Bakshi: The Insurance CloudMASTER®
Powered by Singapore-based Big Data start-up Crayon Data, BigData-MadeSimple.com tapped the insurance industry as being at the forefront of integrating cloud technology into their digital eco system. As stated in…
Understand The Language Of Data: Strata+Hadoop World and TAP
Our world is driven by data. It may speak in whispers, but it can also scream insight and information to those that understand it’s language. This is why I’ll be…
Transformative Training for Hybrid Cloud
Figure 1- Shawn Bolan, Technical Training Manager, New Horizons of Nebraska, https://www.linkedin.com/in/shawn-bolan-96b8a9103 In a recent CloudTech article multi-cloud, or hybrid cloud, strategy was heralded as “…transformative for businesses, allowing them…
Surviving the coming “Hackerpocalypse”
Photo credit: Shutterstock With all the excellent training available on television today, we are all now well prepared to deal with the coming Zombie Apocalypse. Our failure as a society…
4 Factors Driving Digital Transformation ROI
The critical assessment factors for cloud ROI risk probability are the following:
- Infrastructure utilization
- Speed of migration to cloud
- Ability to scale business/mission processes
- Quality delivered by the new cloud-based process
These four factors directly drive digital transformation ROI because they affect revenue, cost, and the time required to realize any investment return. Differences between actual and projected values in these metrics indicate a likely failure to achieve the desired goals.
Although business alignment is always a primary digital transformation drive, ROI remains a key decision component. This metric should, however, be addressed from multiple vantage points to include cloud workload utilization, workload size versus memory/processor distribution and the virtual hardware instance to physical asset ratio.
Value delivered through innovation should also be part of the business value calculation. Value can be delivered through operational cost reductions, optimization of resource capacity, and a reduced total cost of ownership. Business process time reductions, product quality improvements and customer experience enhancements are also useful outcomes.
Security Controls
Business/mission model changes can also introduce operational risk. Acceptance of these risk are based on executive risk tolerance. Their risk mitigation decisions result in the implementation of security controls. A control will restrict a list of possible actions down to what is allowed or permitted by the organization. Encryption, for example, can be used to restrict the unauthorized use of data.
The security control continuum extends over three categories:
- Management (administrative) controls: policies, standards, processes, procedures, and guidelines set by corporate administrative entities (i.e., executive to mid-level management)
- Operational (and physical) controls: operational security (execution of policies, standards and process, education, and awareness) and physical security (facility or infrastructure protection)
- Technical (logical) controls: Access controls, identification and authentication, authorization, confidentiality, integrity, availability, and non-repudiation
They also encompass the following types:
- Directive controls: often referred to as administrative controls, advise employees of the behavior expected of them during their interfaces with or use of information systems
- Preventive controls: include physical, administrative, and technical measures that preclude actions that violate policy or increase the risk to system resources
- Deterrent controls: use warnings and a description of related consequences to prevent security violations
- Compensating controls: Also called an alternative control, a mechanism that is put in place to address security requirements deemed impractical to implement
- Detective controls: Refer to the use of practices, processes, and tools that identify and possibly react to security violations
- Corrective controls: involves physical, administrative, and technical measures designed to react to a security-related incident in order to minimize the opportunity for an unwanted event to reoccur
- Recovery controls: restore the system or operation to a normal operating state once integrity or availability is compromised
The costs associated with the implementation of any security control should be weighed against the value gained from digital transformation business/mission process improvements.
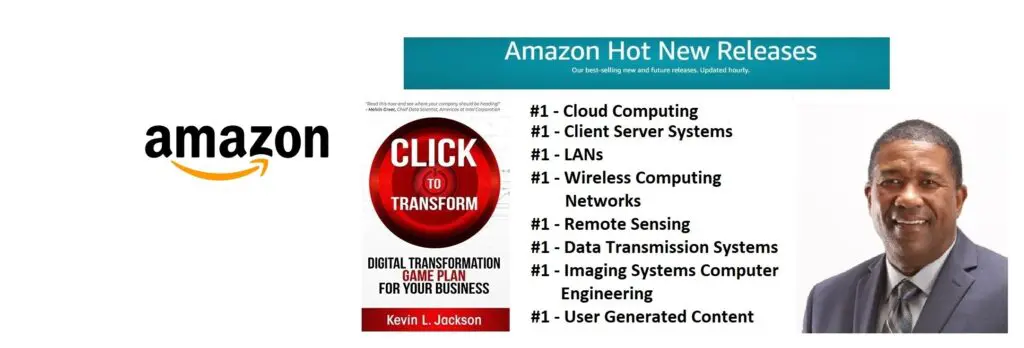
Would you like to learn more about digital transformation innovation? Pick up a copy of my new book, Click to Transform!Â
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
