Twitter Feed
The Time is Now for 21st Century Leadership
I’ve just had the opportunity to preview my good friend Melvin Greer’s newest effort, “21st Century Leadership: Harnessing Innovation, Accelerating Business Success“. Now in pre-release, this book highlights the compelling…
Public Cloud IaaS : A Price/Performance vs. Security Analysis
Industry’s transition from custom made, one-of-a-kind IT infrastructures to the standardize, commodity based cloud paradigm is well on it’s way. IBM’s recent “Under Cloud Cover” study highlights the rapidly of…
Catch the Cloud with DorobekINSIDER LIVE!
Yesterday I thoroughly enjoyed an opportunity to participate in the DorobekINSIDER LIVE edition on cloud computing. The conversation was both lively and informative. Joining me on the show were:…
Cloud Shines Brightly as Future of Disaster Response IT
The call for help began as a rumble. Twenty miles beneath the ocean’s surface, a rupture in a massive tectonic plate ripped a 310 mile-long break in the sea floor,…
NCOIC/NGA Demonstrates Use of Cloud in Disaster Response
When the world’s next major earthquake, tsunami or other disaster hits, military, government and civilian NGA project is available on the NCOIC website. responders will need to manage and…
NBC4 Puts On A Great GovCloud Show !!
NBC 4 in Washington, DC highlighted government cloud computing today as part of their GovInnovate show. Below is just a taste of the informative public service they provided. Go to…
OMB’s Evidence Memo: A Call for Cloud Services Brokerage
by Ray Holloman and Kevin Jackson In a late July memo the Office of Management and Budget requested cloud services brokerage. Well, not in so many words. Rather, OMB requested…
Cloud Services Brokerage Lessons From Alex Rodriguez, Baseball’s Trade Deadline
( A guest post from Ray Holloman, NJVC Corporate Communications) Two stories sat atop baseball’s marquee in the final days of July. The first was the non-waiver trade deadline, baseball’s…
Lessons Learned: VA Cloud Email Termination
According to a Federal Computer Week article by Frank Konkel, The Department of Veterans Affairs terminated its five-year, $36 million cloud computing contract for email and calendaring services with HP…
Deconstructing Cloud: An Excellent Guide to the Cloud Computing World
On an almost daily basis, I’m approach for my views on “cloud computing technology”. Although typically innocent in nature, I always cringe at the thought of enduring yet another hours…
4 Factors Driving Digital Transformation ROI
The critical assessment factors for cloud ROI risk probability are the following:
- Infrastructure utilization
- Speed of migration to cloud
- Ability to scale business/mission processes
- Quality delivered by the new cloud-based process
These four factors directly drive digital transformation ROI because they affect revenue, cost, and the time required to realize any investment return. Differences between actual and projected values in these metrics indicate a likely failure to achieve the desired goals.
Although business alignment is always a primary digital transformation drive, ROI remains a key decision component. This metric should, however, be addressed from multiple vantage points to include cloud workload utilization, workload size versus memory/processor distribution and the virtual hardware instance to physical asset ratio.
Value delivered through innovation should also be part of the business value calculation. Value can be delivered through operational cost reductions, optimization of resource capacity, and a reduced total cost of ownership. Business process time reductions, product quality improvements and customer experience enhancements are also useful outcomes.
Security Controls
Business/mission model changes can also introduce operational risk. Acceptance of these risk are based on executive risk tolerance. Their risk mitigation decisions result in the implementation of security controls. A control will restrict a list of possible actions down to what is allowed or permitted by the organization. Encryption, for example, can be used to restrict the unauthorized use of data.
The security control continuum extends over three categories:
- Management (administrative) controls: policies, standards, processes, procedures, and guidelines set by corporate administrative entities (i.e., executive to mid-level management)
- Operational (and physical) controls: operational security (execution of policies, standards and process, education, and awareness) and physical security (facility or infrastructure protection)
- Technical (logical) controls: Access controls, identification and authentication, authorization, confidentiality, integrity, availability, and non-repudiation
They also encompass the following types:
- Directive controls: often referred to as administrative controls, advise employees of the behavior expected of them during their interfaces with or use of information systems
- Preventive controls: include physical, administrative, and technical measures that preclude actions that violate policy or increase the risk to system resources
- Deterrent controls: use warnings and a description of related consequences to prevent security violations
- Compensating controls: Also called an alternative control, a mechanism that is put in place to address security requirements deemed impractical to implement
- Detective controls: Refer to the use of practices, processes, and tools that identify and possibly react to security violations
- Corrective controls: involves physical, administrative, and technical measures designed to react to a security-related incident in order to minimize the opportunity for an unwanted event to reoccur
- Recovery controls: restore the system or operation to a normal operating state once integrity or availability is compromised
The costs associated with the implementation of any security control should be weighed against the value gained from digital transformation business/mission process improvements.
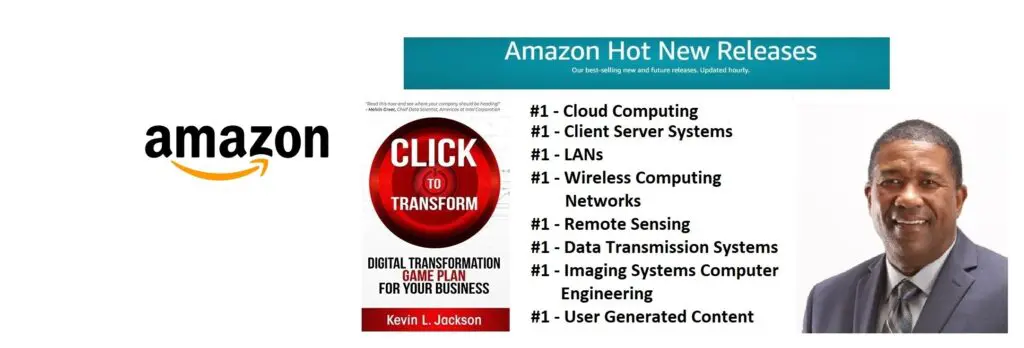
Would you like to learn more about digital transformation innovation? Pick up a copy of my new book, Click to Transform!Â
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
