Twitter Feed
Cloud Computing Evolves: An Interview with Mats Johansson
Recently, Ericsson Digital released an amazing report on Edge Computing and 5G. In it, they explained how distributed cloud computing is paving the way for the future of network communications. They…
The IoT Nexus: Bosch Connected World 2019 in Berlin
Next week, I will be influencing #LikeABosch as I accept an invitation from the company to attend Bosch ConnectedWorld 2019 (BCW19) in Berlin, Germany. This is one of the world’s largest international…
Survive and Thrive With Digital Transformation
First cloud computing then multi-cloud. How can we get ahead of this digital transformation nightmare? These are the laments heard in conference rooms and board meeting around the world. While…
The “George Jetson” of Today
He grew up in Silicon Valley, landed his first job at Apple Computers, was introduced to Nobel Prize winners by his dad and today, he takes a self-driving car…
MWC19: Where Telecommunications and Cloud Meet
As a cloud solution architect, my passion is learning the details about how cloud computing uniquely supports specific business cases. This curiosity is what drove my excitement when Ericsson invited…
Tulane University SoPA Selects “Architechting Cloud Computing Solutions”
Last week, Packt Publishing announced that “Architecting Cloud Computing Solutions” by Kevin L. Jackson and Scott Goessling was selected for use by the Tulane University School of Professional Advancement, Applied Computing Systems & Technology Program as the textbook for…
5G Wireless Technology Connecting Healthcare
Healthcare is in the middle of massive change. Called digital transformation by many, this term describes the industry’s pursuit of the many promises offered by connected patients, connected caregivers, and…
Maria Lensing: The Network Platform for Healthcare’s Future
As a girl, Maria and her family traveled to Memphis, Tennessee to get cancer treatment for her sick brother. The miracle she observed, as the healthcare providers saved her brother’s…
How “Big Iron” Does “Big Regulation”
According to Verizon, there were over there were over 53,000 security incidents in 2017, with over 2,200 of those identified as confirm data breaches. A Ponemon Institute study also showed…
Mainframe Synergies for Digital Transformation
In July of 2018, Broadcom announced its intentions to acquire CA Technologies. In the press release, Hock Tan, President and Chief Executive Officer of Broadcom, said: “This transaction represents an…
4 Factors Driving Digital Transformation ROI
The critical assessment factors for cloud ROI risk probability are the following:
- Infrastructure utilization
- Speed of migration to cloud
- Ability to scale business/mission processes
- Quality delivered by the new cloud-based process
These four factors directly drive digital transformation ROI because they affect revenue, cost, and the time required to realize any investment return. Differences between actual and projected values in these metrics indicate a likely failure to achieve the desired goals.
Although business alignment is always a primary digital transformation drive, ROI remains a key decision component. This metric should, however, be addressed from multiple vantage points to include cloud workload utilization, workload size versus memory/processor distribution and the virtual hardware instance to physical asset ratio.
Value delivered through innovation should also be part of the business value calculation. Value can be delivered through operational cost reductions, optimization of resource capacity, and a reduced total cost of ownership. Business process time reductions, product quality improvements and customer experience enhancements are also useful outcomes.
Security Controls
Business/mission model changes can also introduce operational risk. Acceptance of these risk are based on executive risk tolerance. Their risk mitigation decisions result in the implementation of security controls. A control will restrict a list of possible actions down to what is allowed or permitted by the organization. Encryption, for example, can be used to restrict the unauthorized use of data.
The security control continuum extends over three categories:
- Management (administrative) controls: policies, standards, processes, procedures, and guidelines set by corporate administrative entities (i.e., executive to mid-level management)
- Operational (and physical) controls: operational security (execution of policies, standards and process, education, and awareness) and physical security (facility or infrastructure protection)
- Technical (logical) controls: Access controls, identification and authentication, authorization, confidentiality, integrity, availability, and non-repudiation
They also encompass the following types:
- Directive controls: often referred to as administrative controls, advise employees of the behavior expected of them during their interfaces with or use of information systems
- Preventive controls: include physical, administrative, and technical measures that preclude actions that violate policy or increase the risk to system resources
- Deterrent controls: use warnings and a description of related consequences to prevent security violations
- Compensating controls: Also called an alternative control, a mechanism that is put in place to address security requirements deemed impractical to implement
- Detective controls: Refer to the use of practices, processes, and tools that identify and possibly react to security violations
- Corrective controls: involves physical, administrative, and technical measures designed to react to a security-related incident in order to minimize the opportunity for an unwanted event to reoccur
- Recovery controls: restore the system or operation to a normal operating state once integrity or availability is compromised
The costs associated with the implementation of any security control should be weighed against the value gained from digital transformation business/mission process improvements.
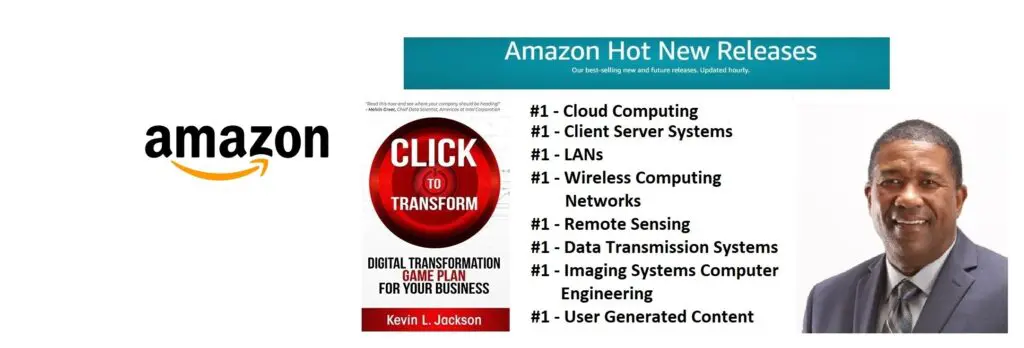
Would you like to learn more about digital transformation innovation? Pick up a copy of my new book, Click to Transform!Â
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes