Twitter Feed
CloudCamp Federal @ FOSE
Sign up now CloudCamp Federal @ FOSE, March 10,2009, 3pm – 8:30pm at the Walter E. Washington Convention Center, 801 Mount Vernon Place NW , Washington, DC. As a follow-up…
Thank You NVTC “Cool Tech” and TechBISNOW !!
Thank you to Dede Haas, Chris D’Errico and the Northern Virginia Technology Council for the opportunity to speak at yesterday’s NVTC “Cool Tech” Committee meeting! The Agilex facilities were awesome…
A Significant Event in Cloud Interoperability
On Jan 20th, GoGrid released it’s API specification under a Creative Commons license. “The Creative Commons Attribution Share Alike 3.0 license, under which the GoGrid cloudcenter API now falls, allows…
Booz|Allen|Hamilton & Dataline Sponsor 2nd Government Cloud Computing Survey
Dataline, Booz|Allen|Hamilton and the Government Cloud Computing Community have teamed together to sponsor the 2nd Government Cloud Computing Survey. Cloud Computing has come a long way since the first survey six months…
Gartner Lays Out 7-year Plan for Cloud Computing
According to Gartner’s new report, cloud computing will go through three phases over seven years before it will mature as an industry; – Phase 1: 2007 to 2011 — Pioneers…
Cloud Interoperability Magazine Launches
My congratulations goes out today to Reuven Cohen on the launch of Cloud Interoperability Magazine. The site will focus on Cloud Computing, standardization efforts, emerging technologies, and infrastructure API’s. As the new…
Why Can’t We Eliminate the “Technology Refresh” RFP?
In order to maintain life cycle and technology, the Navy is upgrading server farms at fifteen (15) sites and any future sites throughout the Far East, Europe and Middle East…
Cloud & the Government Session at Cloud Computing Expo
Earlier this week I announced that I will be presenting at SYS-CON’s 2nd International Cloud Computing Conference & Expo in New York City this coming March 30-April 1, 2009. During…
CSC and Terremark target US Government with Cloud Computing
Today’s announcement by CSC reinforced the strong wave of cloud computing towards the Federal space. Ranked by Washington Technology Magazine as 9th largest (by contract dollar value) government contractor, this…
Should my agency consider using cloud computing?
This is clearly the question on the minds and lips of every government IT decsionmaker in town. Why should a government agency even consider cloud computing? In reality, the decision…
4 Factors Driving Digital Transformation ROI
The critical assessment factors for cloud ROI risk probability are the following:
- Infrastructure utilization
- Speed of migration to cloud
- Ability to scale business/mission processes
- Quality delivered by the new cloud-based process
These four factors directly drive digital transformation ROI because they affect revenue, cost, and the time required to realize any investment return. Differences between actual and projected values in these metrics indicate a likely failure to achieve the desired goals.
Although business alignment is always a primary digital transformation drive, ROI remains a key decision component. This metric should, however, be addressed from multiple vantage points to include cloud workload utilization, workload size versus memory/processor distribution and the virtual hardware instance to physical asset ratio.
Value delivered through innovation should also be part of the business value calculation. Value can be delivered through operational cost reductions, optimization of resource capacity, and a reduced total cost of ownership. Business process time reductions, product quality improvements and customer experience enhancements are also useful outcomes.
Security Controls
Business/mission model changes can also introduce operational risk. Acceptance of these risk are based on executive risk tolerance. Their risk mitigation decisions result in the implementation of security controls. A control will restrict a list of possible actions down to what is allowed or permitted by the organization. Encryption, for example, can be used to restrict the unauthorized use of data.
The security control continuum extends over three categories:
- Management (administrative) controls: policies, standards, processes, procedures, and guidelines set by corporate administrative entities (i.e., executive to mid-level management)
- Operational (and physical) controls: operational security (execution of policies, standards and process, education, and awareness) and physical security (facility or infrastructure protection)
- Technical (logical) controls: Access controls, identification and authentication, authorization, confidentiality, integrity, availability, and non-repudiation
They also encompass the following types:
- Directive controls: often referred to as administrative controls, advise employees of the behavior expected of them during their interfaces with or use of information systems
- Preventive controls: include physical, administrative, and technical measures that preclude actions that violate policy or increase the risk to system resources
- Deterrent controls: use warnings and a description of related consequences to prevent security violations
- Compensating controls: Also called an alternative control, a mechanism that is put in place to address security requirements deemed impractical to implement
- Detective controls: Refer to the use of practices, processes, and tools that identify and possibly react to security violations
- Corrective controls: involves physical, administrative, and technical measures designed to react to a security-related incident in order to minimize the opportunity for an unwanted event to reoccur
- Recovery controls: restore the system or operation to a normal operating state once integrity or availability is compromised
The costs associated with the implementation of any security control should be weighed against the value gained from digital transformation business/mission process improvements.
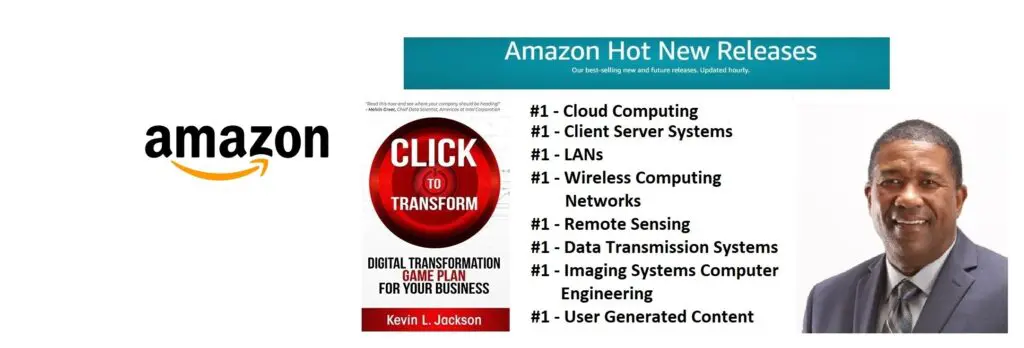
Would you like to learn more about digital transformation innovation? Pick up a copy of my new book, Click to Transform!Â
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
