Twitter Feed
Cloud computing: A data-centric business model
According to the National Institute of Standards and Technology: “Cloud computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers,…
John Mayer At Dell World 2015!! (Oh, I’ll be there too.)
An artist who defies all boundaries, John Mayer has won seven Grammy Awards and sold more than 17 million albums worldwide. The singer, songwriter and guitarist’s skills have been widely…
Data-centric Security: The New Must Have
Where is your data right now? The explosion of cloud computing and consumer IT means that your data, as well as data about you, can be virtually anywhere.Having your data and the…
Personal email:Pathway to Cybersecurity Breaches
As a business communications tool, email is the dominant option, and many corporations have policies that allow the use of personal email on corporate computers. In a recent Adobe Systems…
IEEE Cloud Computing: Legal Clouds
The new issue of IEEE Cloud Computing is now available! This special issue looks at how to balance privacy with legitimate surveillance and lawful data access. Some of the…
Cloud hosting: Look beyond cost savings and weigh pros, cons
Is your company struggling with the idea of using “cloud hosting” in order to save money? Truth be known, using cost savings as the primary reason for moving to cloud…
“Cloud First” Lessons Learned from ViON
In 2011, then United States CIO Vivek Kundra released the US Federal Cloud Computing Strategy [1]. In the executive summary he pointed to cloud computing as a key component of…
Looking for Security Peak Performance?
You can find it at Dell Peak Performance 2015!!! I’ll be there at the Aria Resort and Casino in Las Vegas attending as a social media correspondent with a full…
The Cybersecurity Sprint: Are we safe yet?
UPDATE: NBC News reports U.S. officials have disclosed a hack of the Pentagon’s Joint Staff unclassified email system, which took place on July 25. Recent unauthorized access to a U.S. government database…
Cloud Computing + Things = “Information Excellence”, Not IoT
The Internet of Things (IoT) has quickly become the next “be all to end all” in information technology. Touted as how cloud computing will connect everyday things together, it is…
The Achilles heel of every transformative business model is their reliance on ever increasing amounts of data that need to be transported quickly across wide area networks and processed at edge computing end points. To meet this expected demand, the global telecommunications industry is rapidly moving toward a future in which networks must have the agility, flexibility, and scalability to deliver aggregated capabilities through fully programmable networks.
Since the late 1970s, new generations of technology and wireless standards have been introduced every decade through the current transition between 4G and 5G capabilities. Limited data capability was provided using circuit-switching under the European Telecommunications Standards Institute (ETSI) Global System for Mobile Communications (GSM) standard. Improved data rates were brought to the market in the late 1990s by using 2.5G and 2.75G technology, which were named GPRS (general packet radio service) and EDGE (enhanced data rates for GSM Evolution). The introduction of the LTE network later set the standard for high-speed wireless communications on mobile devices and data terminals.
Historically, sovereign nations have managed their telecommunications networks as national assets.
The political negotiations that drove that history led to underlying technological choices and today’s
heated international competition around 5G network deployments. In fact, western nations fear that China’s Huawei Technologies’ dominance of 5G technology could give the Chinese government backdoor access to Western mobile networks and the application. This international competition will determine the availability of specific technologies and telecommunications resources in each geographic region.
For 5G networks, data transfer speed, volume, and latency depend on the spectrum bands used and the network usage context (fixed or mobile). MmWave spectrum is a high-frequency technology that lies between 30 GHz and 300 GHz. It is attractive because its shorter wavelengths create narrower beams, which provides better resolution and security for data transmission. A 5G mmWave system requires a significant infrastructure build but could reap the benefits of data transferred at up to twenty times the speed of current 4G LTE networks. MIMO (multiple-input and multiple-output) increases throughput by using high-quality signals to receive multiple data streams at a reduced power per stream. Massive MIMO can multiply the capacity of a wireless connection without requiring more spectrum, which could potentially deliver a fifty-fold increase in the future.
These network capabilities are substantially superior to previous wireless technology generations and have subsequently set off the rapid development of many new application requirements and functions. With this new infrastructure, application components are placed in an optimal location to use compute and data storage services of the distributed cloud. The distributed cloud approach increases capacity, availability, and coverage while also limiting data transfer requirements. A distributed cloud solution enables edge computing by using micro and small data centers. Application developers must learn how to exploit these new design requirements to deliver ever increasing value to their end users.
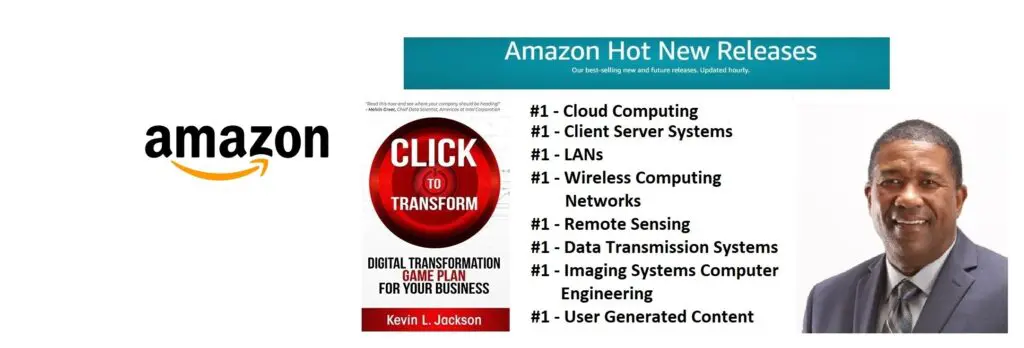
Learn more about digital transformation innovation: pick up a copy of my new book, Click to Transform!Â
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
