Twitter Feed
NJVC to Spotlight Cloudcuity at Gartner Data Center Conference
Las Vegas., Nov. 15, 2012 — NJVC, an information technology solutions provider headquartered in Northern Virginia, announces it will spotlight its Cloudcuity™ framework for delivering secure and unified cloud management…
NJVC Cloud Expert Kevin L. Jackson Launches Second Book: GovCloud II: Implementation and Cloud Brokerage Services
VIENNA, Va., Nov. 8, 2012—NJVC, an information technology (IT) solutions provider headquartered in northern Virginia, is pleased to announce that Kevin L. Jackson, vice president and general manager, cloud services,…
Virtustream a Visionary in Gartner 2012 IaaS Magic Quadrant
Congratulations to NJVC Cloudcuity partner Virtustream for being positioned as a visionary in the Gartner 2012 IaaS Magic Quadrant! Magic Quadrants provide a graphical competitive positioning of four types of…
GovCloud II: Implementation and Cloud Brokerage Services Now Available
I’m happy and proud to announce the release of my second book, “GovCloud II: Implementation and Cloud Brokerage Services” by my publisher Government Training Inc. The public and private…
NJVC® Introduces Cloudcuity™ AppDeployer to Create and Sell Software Applications
Developers Can Create, Deploy and Publish Apps in the Cloud for Free Vienna, Va., Oct. 18, 2012 — NJVC®, an information technology (IT) solutions provider headquartered in Northern Virginia, introduces…
NJVC® Announces the Cloudcuity™ Government Marketplace, Powered by Virtustream’s Secure Cloud xChange
Vienna, Va., Oct. 4, 2012—NJVC®, an information technology solutions provider headquartered in Northern Virginia, and Virtustream, Inc., a leading enterprise cloud software company, today announced a new alliance to provide…
Cloudcuity™: Thought Leadership Translated to Operational Excellence
As my long time readers have certainly noticed, the frequency of my posts have lengthened over the past few months. First, I would like to offer my apologies for being…
NJVC® Unveils Cloudcuity™ Umbrella Framework for NJVC Cloud Services
Vienna, Va., Sept. 13, 2012 — NJVC®, an information technology (IT) solutions provider headquartered in Northern Virginia, introduces Cloudcuity™, a new framework for the company’s cloud service offerings to help…
NJVC® Announces SaaS Accelerate: Specialized Infrastructure Hosting and Managed Services Program for Software-as-a-Service Providers
VIENNA, Va., Aug. 15, 2012 —NJVC® announces the release of NJVC SaaS Accelerate, a specialized infrastructure hosting and managed services offering designed to support the business needs of software-as-a-service (SaaS)…
Texas Cloud Computing Lessons Learned
Late last week the Texas Department of Information Resources (DIR) released an important whitepaper that reviewed it’s multi-year Pilot Texas Cloud Offering (PTCO). This project was designed to allow a…
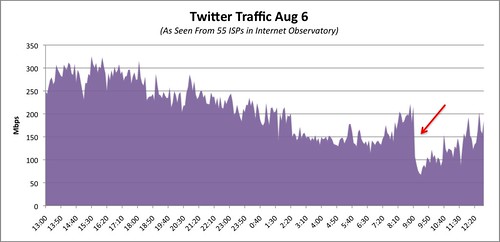
If I were a betting man, I’d say that this attack was done using Multi-Stage BGP & DNS Attack Vector. My only real proof is a little common sense as well as the simple reason that a typical HTTP denial of service attack causes a spike in traffic not a drop as illustrated below.
( Thank you. If you enjoyed this article, get free updates by email or RSS – KLJ )
1 Comments
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes


This is so sad.