Twitter Feed
Thank You GetVoIP!!
Thank you for the honor of being named a “Top 100 Cloud Professionals to Follow on G+”! Congratulations also to my 99 colleagues. Read more at: ↑ Grab this Headline…
Facilitators Announced For NGA Agile Cloud Brainstorming Event
The Information Technology Acquisition Advisory Council (ITAAC) and the Telecommunications Industry Association (TIA) are announcing a slate of innovative leaders to serve as facilitators for the upcoming “Agile Sourcing Environment…
MBO Partners Spotlights GovCloud Founder Kevin L. Jackson
Associate Spotlight Interview with Kevin L. JacksonMBO Associate Since 10/2013 1) Tell us a little bit about what you do.I am the CEO and founder of GovCloud Network, LLC. In…
ITAAC/ICH and TIA To Host Commercial Cloud Sourcing Brainstorming Session for NGA
The Information Technology Acquisition Advisory Council (ITAAC) and Telecommunications Industry Association (TIA) are honored to team with NGA in hosting the first “Agile Sourcing Environment for Commercial Cloud” brainstorming session,…
Author and Tech Strategist Melvin Greer Profiled by WashingtonExec
Congratulations to my NCOIC colleague and dear friend Melvin Greer on his impressive WashingtonExec interview. A senior fellow and chief strategist at Lockheed Martin, Mel has more than 29 years’…
IT Risk Management Summit – March 26, 2013 – Reston, VA
In response to growing demand for formal software risk and quality management tools, the nations’ most respected standards bodies and IT communities of practice have joined forces to advance the…
PerspecSys Survey Reveals Cloud-based Security Concerns for 2014
Today PerspecSys announced the results of a survey conducted at the 2014 RSA Conference concerning the attitudes and policies of organizations towards cloud-based security. After polling 130 security professionals on…
NCOIC Debuts Roadmap for Designing, Managing Cyber-secure Hybrid Computing Environment
Open process by the Network Centric Operations Industry Consortium uses cloud infrastructure to cut computing costs in half and enable collaboration by different systems and users WASHINGTON—March 5, 2014—The Network…
Why State & Local Governments Should be Prepared for Cloud
You are invited to attend the Cloud Webinar Series: Why State & Local Governments Should be Prepared for Cloud. This educational webinar is brought to you by RISC Networks, and…
IBM Hybrid Cloud Debate: Experts debate: Are Hybrid Clouds the End All Be All?
A hybrid cloud may become the solution as the debate between public vs private cloud becomes so 2013. The industry’s experts will debate on when the hybrid clouds are and…
4 Factors Driving Digital Transformation ROI
The critical assessment factors for cloud ROI risk probability are the following:
- Infrastructure utilization
- Speed of migration to cloud
- Ability to scale business/mission processes
- Quality delivered by the new cloud-based process
These four factors directly drive digital transformation ROI because they affect revenue, cost, and the time required to realize any investment return. Differences between actual and projected values in these metrics indicate a likely failure to achieve the desired goals.
Although business alignment is always a primary digital transformation drive, ROI remains a key decision component. This metric should, however, be addressed from multiple vantage points to include cloud workload utilization, workload size versus memory/processor distribution and the virtual hardware instance to physical asset ratio.
Value delivered through innovation should also be part of the business value calculation. Value can be delivered through operational cost reductions, optimization of resource capacity, and a reduced total cost of ownership. Business process time reductions, product quality improvements and customer experience enhancements are also useful outcomes.
Security Controls
Business/mission model changes can also introduce operational risk. Acceptance of these risk are based on executive risk tolerance. Their risk mitigation decisions result in the implementation of security controls. A control will restrict a list of possible actions down to what is allowed or permitted by the organization. Encryption, for example, can be used to restrict the unauthorized use of data.
The security control continuum extends over three categories:
- Management (administrative) controls: policies, standards, processes, procedures, and guidelines set by corporate administrative entities (i.e., executive to mid-level management)
- Operational (and physical) controls: operational security (execution of policies, standards and process, education, and awareness) and physical security (facility or infrastructure protection)
- Technical (logical) controls: Access controls, identification and authentication, authorization, confidentiality, integrity, availability, and non-repudiation
They also encompass the following types:
- Directive controls: often referred to as administrative controls, advise employees of the behavior expected of them during their interfaces with or use of information systems
- Preventive controls: include physical, administrative, and technical measures that preclude actions that violate policy or increase the risk to system resources
- Deterrent controls: use warnings and a description of related consequences to prevent security violations
- Compensating controls: Also called an alternative control, a mechanism that is put in place to address security requirements deemed impractical to implement
- Detective controls: Refer to the use of practices, processes, and tools that identify and possibly react to security violations
- Corrective controls: involves physical, administrative, and technical measures designed to react to a security-related incident in order to minimize the opportunity for an unwanted event to reoccur
- Recovery controls: restore the system or operation to a normal operating state once integrity or availability is compromised
The costs associated with the implementation of any security control should be weighed against the value gained from digital transformation business/mission process improvements.
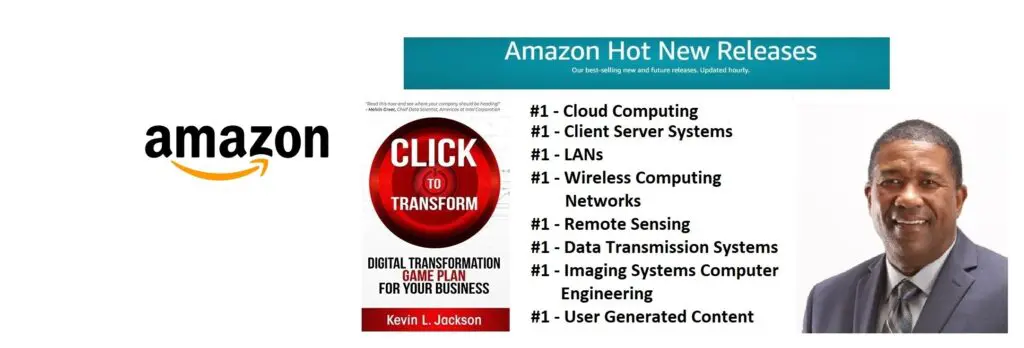
Would you like to learn more about digital transformation innovation? Pick up a copy of my new book, Click to Transform!Â
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
