Twitter Feed
Amazon’s Jeff Bezos on Cloud Computing
Amazon’s Jeff Bezos on Cloud Computing How and when Amazon began its cloud computing effort.Why Amazon has become an innovator with Amazon Web Services and how it relates to their…
Dataline, IBM, Google, Northrop Grumman on Cloud Computing
My company, Dataline LLC, in cooperation with IBM, Google and Northrop Grumman Mission Systems, is sponsoring an educational series entitled “Cloud Computing in a Netcentric Environment“. The series will be…
EMC Studies Cloud Computing Security
Storage firm EMC has joined the Daoli Trusted Infrastructure Project which conducts research into “trust and assurance” in cloud computing environments. The team’s research will focus on cloud computing, trusted…
The Cloud Computing Marketplace
For explaination and details see Understanding the Cloud Computing/SaaS/PaaS markets: a Map of the Players in the Industry by Peter Laird, Kent Dickson, and Steve Bobrowski from Oracle. Update: Please…
Key cloud computing concerns by CXO’s
Key cloud computing concerns by CXO’s attending the Enterprise 2.0 Conference in Boston were addresed in a June 9th panel of executives from Google, Amazon Web Services (AWS), and Salesforce.com.…
IBM Cloud Computing Center
On June 5th, IBM announced it will establish the first Cloud Computing Center for software companies in China, which will be situated at the new Wuxi Tai Hu New Town…
EUCALYPTUS – An Open Source Cloud Computing Platform
Elastic Utility Computing Architecture for Linking Your Programs To Useful Systems (EUCALYPTUS) is a new project that seems to be trying to put an “open source” flavor to cloud computing.…
The Honorable John G. Grimes Speaks about Cloud Computing
Today I had the pleasure of hearing The Honorable John G. Grimes, Assistant Secretary of Defense for Networks and Information Intergration and Department of Defense CIO, speak on some key…
Amazon leads Google into the cloud (So what else is new)
In this May 1, 2008 Globe and Mail Update article, Mathew Ingram provides an excellent comparison of Amazon and Google’s cloud computing initiatives. Bottom line: Amazon leads the pack with…
Web 2.0 Expo – What is Cloud Computing?
For some interesting views, take a look at these video interviews on what is cloud computing. These were done during the recent Web 2.0 Expo, April 22-25 in San Francisco,…
4 Factors Driving Digital Transformation ROI
The critical assessment factors for cloud ROI risk probability are the following:
- Infrastructure utilization
- Speed of migration to cloud
- Ability to scale business/mission processes
- Quality delivered by the new cloud-based process
These four factors directly drive digital transformation ROI because they affect revenue, cost, and the time required to realize any investment return. Differences between actual and projected values in these metrics indicate a likely failure to achieve the desired goals.
Although business alignment is always a primary digital transformation drive, ROI remains a key decision component. This metric should, however, be addressed from multiple vantage points to include cloud workload utilization, workload size versus memory/processor distribution and the virtual hardware instance to physical asset ratio.
Value delivered through innovation should also be part of the business value calculation. Value can be delivered through operational cost reductions, optimization of resource capacity, and a reduced total cost of ownership. Business process time reductions, product quality improvements and customer experience enhancements are also useful outcomes.
Security Controls
Business/mission model changes can also introduce operational risk. Acceptance of these risk are based on executive risk tolerance. Their risk mitigation decisions result in the implementation of security controls. A control will restrict a list of possible actions down to what is allowed or permitted by the organization. Encryption, for example, can be used to restrict the unauthorized use of data.
The security control continuum extends over three categories:
- Management (administrative) controls: policies, standards, processes, procedures, and guidelines set by corporate administrative entities (i.e., executive to mid-level management)
- Operational (and physical) controls: operational security (execution of policies, standards and process, education, and awareness) and physical security (facility or infrastructure protection)
- Technical (logical) controls: Access controls, identification and authentication, authorization, confidentiality, integrity, availability, and non-repudiation
They also encompass the following types:
- Directive controls: often referred to as administrative controls, advise employees of the behavior expected of them during their interfaces with or use of information systems
- Preventive controls: include physical, administrative, and technical measures that preclude actions that violate policy or increase the risk to system resources
- Deterrent controls: use warnings and a description of related consequences to prevent security violations
- Compensating controls: Also called an alternative control, a mechanism that is put in place to address security requirements deemed impractical to implement
- Detective controls: Refer to the use of practices, processes, and tools that identify and possibly react to security violations
- Corrective controls: involves physical, administrative, and technical measures designed to react to a security-related incident in order to minimize the opportunity for an unwanted event to reoccur
- Recovery controls: restore the system or operation to a normal operating state once integrity or availability is compromised
The costs associated with the implementation of any security control should be weighed against the value gained from digital transformation business/mission process improvements.
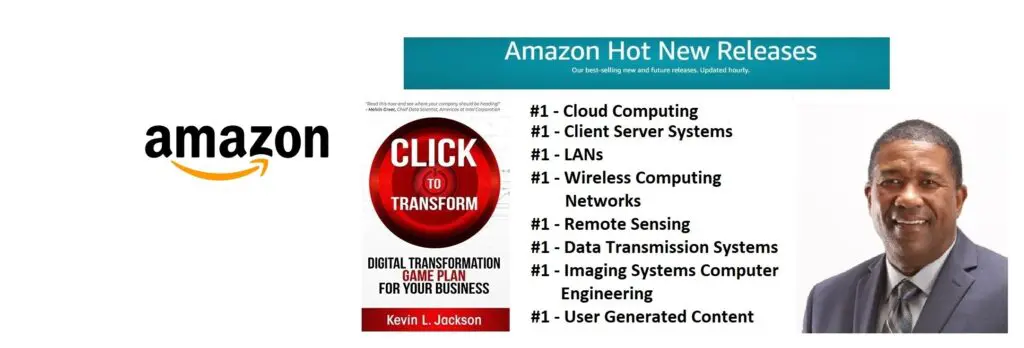
Would you like to learn more about digital transformation innovation? Pick up a copy of my new book, Click to Transform!Â
Cloud Computing
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- Route1 Announces Q2 2019 Financial Results
- CPUcoin Expands CPU/GPU Power Sharing with Cudo Ventures Enterprise Network Partnership
- ChannelAdvisor to Present at the D.A. Davidson 18th Annual Technology Conference
Cybersecurity
- Route1 Announces Q2 2019 Financial Results
- FIRST US BANCSHARES, INC. DECLARES CASH DIVIDEND
- Business Continuity Management Planning Solution Market is Expected to Grow ~ US$ 1.6 Bn by the end of 2029 - PMR
- Atos delivers Quantum-Learning-as-a-Service to Xofia to enable artificial intelligence solutions
- New Ares IoT Botnet discovered on Android OS based Set-Top Boxes
